 |
市场调查报告书
商品编码
1642055
异常检测:市场占有率分析、产业趋势与统计、成长预测(2025-2030)Anomaly Detection - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030) |
||||||
※ 本网页内容可能与最新版本有所差异。详细情况请与我们联繫。
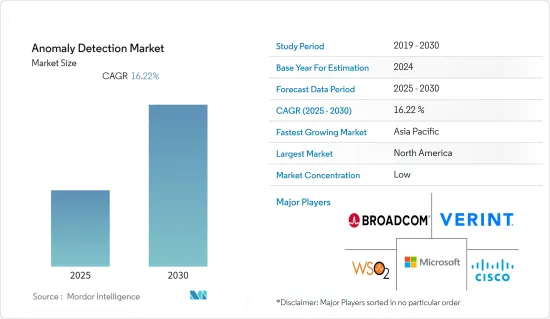
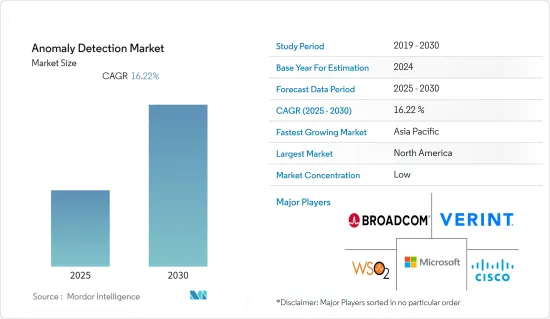
预测期内,异常检测市场预计将以 16.22% 的复合年增长率成长。
传统统计方法正在被生成对抗网路 (GAN)、变分自动编码器 (Vaes) 和循环神经网路 (RNN) 等现代技术所取代,这些技术增强了各种系统中异常的识别能力。此外,对大规模资料储存设施和即时分析的需求不断增长,推动了异常检测系统的采用。
主要亮点
- 异常检测涉及识别表明业务或流程发生异常变化的异常,而不是遵循可预测的资料或模式。除了诈欺侦测、系统健康监控和入侵侦测之外,异常侦测还可用于其他目的。
- 随着连网装置数量的快速成长,它们产生的资料量非常庞大,管理这些资讯已成为一项重大挑战。异常检测可能会克服这一差距并在预测期内促进市场成长。
- 资料外洩通常意味着消费者身分被盗。一旦受到攻击,诈骗就可以进行诈欺购买、更改清单资讯、建立虚假评论、更改帐户资料以及向银行帐户付款。
- 由于这种成长,异常检测市场预计将在预测期内成长,多种连网设备将用于银行和金融服务、医疗保健、製造业、IT 和通讯、国防和政府等领域。
- 预测期内异常检测成长面临的主要挑战是成本上升和来自开放原始码替代品的竞争,这可能会使组织难以采用这些工具和解决方案。
异常检测市场趋势
BFSI 预计将占据大部分市场占有率
- 由于广泛的网路框架和敏感的客户讯息,BFSI 行业面临多次资料外洩和网路攻击。因此,行业内的公司正在寻找替代解决方案,这可能会在预测期内加强异常检测市场。
- 业务涉及银行员工、客户和海外代理商进行的广泛活动和交易。鑑于这些活动的复杂性,需要持续监控以确保银行及其最终客户不会受到此类恶意活动的严重打击。基于这些原因,组织正在开发解决方案和服务来检测异常。
- 业务涉及银行员工、客户和独立机构所进行的一系列常规和非常规活动和交易。这些活动的性质很难描述。需要持续监控以避免各种可能对银行及其客户造成不利影响的不适当和不规则活动。因此,在该领域提供解决方案和服务的公司有巨大的机会缓解这些异常现象。
- 此外,数位化程度的提高使银行和金融机构能够透过线上入口网站更有效率地提供银行服务,从而提供更好的客户服务。因此,产生了大量资料,安全地处理这些关键资讯变得至关重要。
北美占最大市场份额
- 美国联邦贸易委员会(FTC)指出,与付款和银行服务相关的身份盗窃在美国十分普遍,这可能导致更广泛地采用异常检测解决方案和服务。
- 北美率先推行自带装置 (BYOD) 文化,推动了 BYOD 的广泛采用。因此,主要企业开始寻找能够确保业务相关资讯安全的解决方案和服务,这可能会导致该地区异常检测市场的扩大。
- 区域性公司为其客户提供异常检测领域更广泛的解决方案,提供更先进的功能和特性。
- 此外,该全部区域互联设备数量的不断增加,加上诈骗和网路攻击的发生率不断上升,推动了对异常检测的需求,加速了该领域的市场成长。
- 线上演算法、学习增量方法、滑动技术等异常检测系统的采用是各个领域用于高效传输资料的最新基于批次视窗的异常检测技术,并且受到对大容量资料储存单元和即时资料分析的需求的推动。
异常检测行业概况
Cisco、WSO2 和微软等主要企业主导着异常检测市场竞争。整体来看,一个产业内竞争对手之间的敌意比较高。透过策略联盟、合併和收购,市场参与者可以立足于为客户提供更好的解决方案和产品。
今年 6 月,思科宣布了「思科网路云端」的愿景,这是一个支援内部部署和云端营运模式的整合管理平台。这些创新包括 SSO、API 金钥交换/储存库、永续资料中心网路解决方案以及透过 Cisco ThousandEyes 扩展的网路保证。思科网路云端透过更灵活的思科 Catalyst 交换器堆迭、增强的资料中心电力和能源消耗可视性以及可提高网路营运商效能和视觉性的新 AI资料中心蓝图,大大简化了 IT。
两家公司于 3 月宣布扩大伙伴关係,透过将 Google Cloud Contact Center AI 与 Verint 的客户参与平台结合,协助提高客服中心的效能。 Verint 的客户经验自动化解决方案与 Google Cloud 的 Contact Center AICCAI 平台的结合非常无缝,Verint 平台独特的开放式架构也是如此。透过此次合作,企业可以使用 Verint 解决方案透过 CX 自动化来缩小参与能力差距。这种强大的跨平台方法为寻求最佳解决方案的组织提供了必要的功能。
其他福利:
- Excel 格式的市场预测 (ME) 表
- 3 个月的分析师支持
目录
第 1 章 简介
- 研究假设和市场定义
- 研究范围
第二章调查方法
第三章执行摘要
第四章 市场洞察
- 市场概况
- 产业吸引力-波特五力分析
- 供应商的议价能力
- 购买者/消费者的议价能力
- 新进入者的威胁
- 替代品的威胁
- 竞争对手之间的竞争
第五章 市场动态
- 市场驱动因素
- 网路犯罪的兴起
- 软体测试中越来越多地采用异常检测解决方案
- 市场限制
- 开放原始码替代品构成威胁
第六章 市场细分
- 按类型
- 解决方案
- 服务
- 按最终用户产业
- BFSI
- 製造业
- 卫生保健
- 资讯科技/通讯
- 其他最终用户产业
- 按部署
- 本地
- 云
- 按地区
- 北美洲
- 美国
- 加拿大
- 欧洲
- 英国
- 德国
- 法国
- 亚洲
- 澳洲
- 日本
- 印度
- 拉丁美洲
- 中东和非洲
- 北美洲
第七章 竞争格局
- 公司简介
- Verint Systems Inc.
- Broadcom Inc.(Symantec Corporation)
- WSO2 Inc.
- Microsoft Corporation
- Cisco Systems Inc.
- IBM Corporation
- Wipro Limited
- Trend Micro Incorporated
- SAS Institute Inc.
- Happiest Minds Technologies Pvt. Ltd
- Guardian Analytics Inc.
第八章投资分析
第九章 市场机会与未来趋势
The Anomaly Detection Market is expected to register a CAGR of 16.22% during the forecast period.
The traditional statistical approaches are being replaced with modern methods, such as Generative Adversarial Networks (GAN), variational autoencoders (Vaes), and Recurrent Neural Networks (RNNs), thereby enhancing the identification of anomalies across various systems. In addition, the adoption of anomaly detection systems has been increased by a growing demand for significant data storage devices and real-time analysis.
Key Highlights
- Anomaly detection is the identification of anomalies that indicate unusual shifts in operations and processes rather than following predictable data or patterns. In addition to fraud detection, system health monitoring, and intrusion detection, anomaly detection can be used for other purposes.
- As the number of connected devices increases rapidly, the amount of data generated by these devices is enormous, making it a critical task to manage this information, which could lead to the loss of valuable information. Anomaly detection could overcome this gap, increasing market growth during the forecast period.
- The breach of data usually means identity theft to the consumer. Fraudsters can make fraudulent purchases, modify listing information, create false reviews, or change account data to take payments into their bank accounts once compromised.
- The market for anomaly detection As a result of this increase, it is expected to grow during the forecast period, and several connected devices are in sectors such as banking, financial services, health care, manufacturing, information technology, telecommunications, defense, and government.
- The main challenges to the growth of anomaly detection during that period are expected to be rising costs and competition from opensource alternatives, which would make it more difficult for organizations to adopt tools and solutions while there is also a lack of qualified workers in areas such as solution development and incidence of asymmetrical faults within Open Source models.
Anomaly Detection Market Trends
BFSI is Expected to Hold a Significant Part of the Market Share
- It faces several data breaches and cyber attacks due to its extensive network framework and essential customer information in the BFSI sector. Consequently, companies within the industry have been looking for alternate solutions that will likely strengthen the anomaly detection market during the forecast period.
- The banking operation includes various activities and transactions carried out by staff, customers, and foreign agents. Given the complexities of these activities, continuous monitoring is required to ensure that a bank or its end customers are hit significantly by any such malicious activity. For these reasons, solutions and services for detecting anomalies are being developed by organizations.
- Several periodic and occasional activities and transactions carried out by staff, clients, and independent agencies shall be included in banking operations. It is very difficult to describe the nature of these activities. It calls for continuous monitoring to avoid an adverse effect on the bank or its customers due to various inappropriate and random actions. Therefore, firms offering solutions and services in this area have a huge opportunity to mitigate these anomalies.
- In addition, the increase in digitization has enabled banks and financial institutions to offer banking services more efficiently through online portals, allowing them to provide better customer service. This has led to the development of large quantities of data, making it vital that critical information be handled safely and securely.
North America Holds the Largest Share in the Market
- The Federal Trade Commission pointed out that identity theft related to payment and banking services in the United States is widespread, which could lead to increased adoption of Anomaly Detection Solutions and Services.
- North America is a pioneer in the bring-your-own-device (BYOD) culture, which has resulted in its wide-scale adoption. In doing so, the companies have started searching for solutions and services that enable them to guarantee the security of information relating to business, which could lead to an increase in the area's Anomaly Detection Market.
- Regional enterprises provide their clients with an extensive range of solutions in the area of anomaly detection and are providing more advanced features and functionalities.
- In addition, there is also a strong demand for anomaly detection and an acceleration of market growth in this area due to the increasing number of interconnected devices and rising incidences of fraud and cyber-attacks throughout the region.
- Adopting anomaly detection systems as online algorithms, learning incremental approaches, and sliding techniques are among the modern batch window-based anomaly detection techniques used by different sectors to stream data efficiently has been stimulated by the need for large data storage units and real-time data analysis.
Anomaly Detection Industry Overview
Some key players, such as Cisco Systems Inc., WSO2 Inc., Microsoft Corporation, etc., govern the anomaly detection market competition. Overall, the competitive rivalry within the industry is relatively high. Through strategic partnerships, mergers, and acquisitions, the companies in the market can maintain their foothold to provide better solutions and products to their customers.
Cisco announced its vision for Cisco Networking Cloud, an integrated management platform experience for both on-premise and cloud operating models, in June this year. These innovations include SSO, API key exchange/repository, sustainable data center networking solutions, and expanded network assurance with Cisco ThousandEyes.Cisco Networking Cloud will dramatically simplify IT with a more flexible Cisco Catalyst switch stack, improved visibility into data center power and energy consumption, and new AI data center blueprints to enhance performance and visibility for network operators.
Through Google Cloud Contact Center AI integration with Verint's customer engagement Platform, the two companies have announced an enhanced partnership to help improve contact center performance in March this year. Combining its customer experience automation solutions with Google Cloud's Contact Center AICCAI platform is as seamless as the Verint Platform's unique open architecture. Through this collaboration, organizations can use Verint's solutions to close the Engagement capacity gap with CX automation. This robust platform-to-platform approach offers essential capabilities for organizations seeking best-of-breed solutions.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET INSIGHTS
- 4.1 Market Overview
- 4.2 Industry Attractiveness - Porter's Five Forces Analysis
- 4.2.1 Bargaining Power of Suppliers
- 4.2.2 Bargaining Power of Buyers/Consumers
- 4.2.3 Threat of New Entrants
- 4.2.4 Threat of Substitute Products
- 4.2.5 Intensity of Competitive Rivalry
5 MARKET DYNAMICS
- 5.1 Market Drivers
- 5.1.1 Increasing Number of Cyber Crimes
- 5.1.2 Increasing Adoption of Anomaly Detection Solutions in Software Testing
- 5.2 Market Restraints
- 5.2.1 Open Source Alternatives Pose as a Threat
6 MARKET SEGMENTATION
- 6.1 By Type
- 6.1.1 Solutions
- 6.1.2 Service
- 6.2 By End-user Industry
- 6.2.1 BFSI
- 6.2.2 Manufacturing
- 6.2.3 Healthcare
- 6.2.4 IT and Telecommunications
- 6.2.5 Other End-user Industries
- 6.3 By Deployment
- 6.3.1 On-premise
- 6.3.2 Cloud
- 6.4 By Geography
- 6.4.1 North America
- 6.4.1.1 United States
- 6.4.1.2 Canada
- 6.4.2 Europe
- 6.4.2.1 United Kingdom
- 6.4.2.2 Germany
- 6.4.2.3 France
- 6.4.3 Asia
- 6.4.3.1 Australia
- 6.4.3.2 Japan
- 6.4.3.3 India
- 6.4.4 Latin America
- 6.4.5 Middle East and Africa
- 6.4.1 North America
7 COMPETITIVE LANDSCAPE
- 7.1 Company Profiles
- 7.1.1 Verint Systems Inc.
- 7.1.2 Broadcom Inc. (Symantec Corporation)
- 7.1.3 WSO2 Inc.
- 7.1.4 Microsoft Corporation
- 7.1.5 Cisco Systems Inc.
- 7.1.6 IBM Corporation
- 7.1.7 Wipro Limited
- 7.1.8 Trend Micro Incorporated
- 7.1.9 SAS Institute Inc.
- 7.1.10 Happiest Minds Technologies Pvt. Ltd
- 7.1.11 Guardian Analytics Inc.






