 |
市场调查报告书
商品编码
1937396
非洲网路安全:市场占有率分析、产业趋势与统计、成长预测(2026-2031 年)Africa Cybersecurity - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2026 - 2031) |
||||||
※ 本网页内容可能与最新版本有所差异。详细情况请与我们联繫。
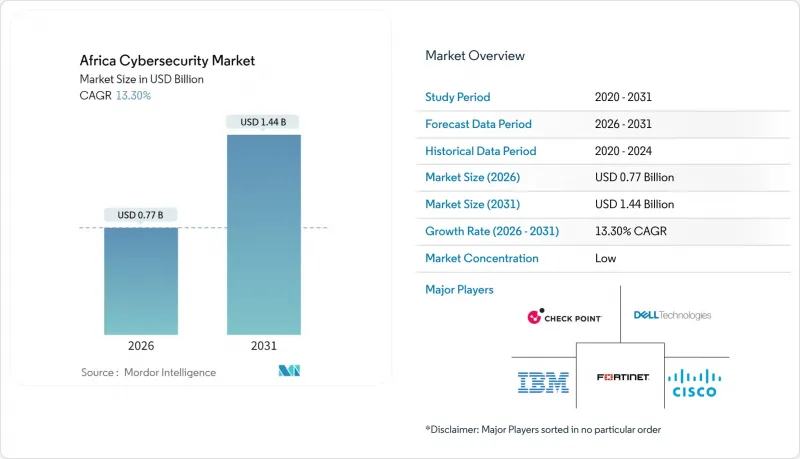
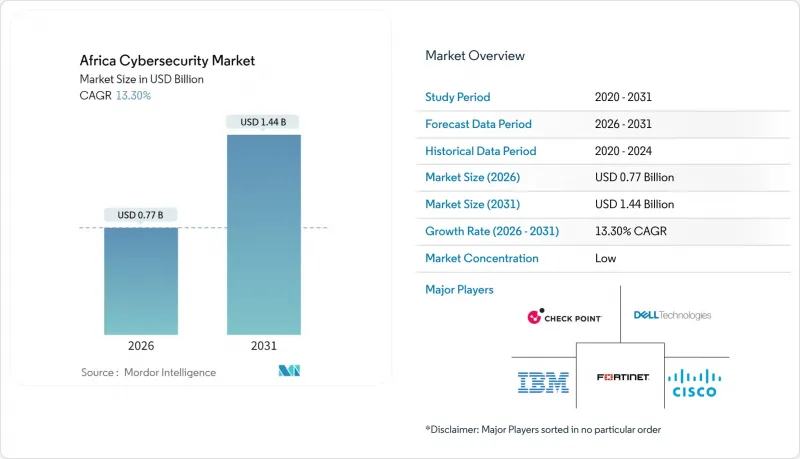
预计非洲网路安全市场将从 2025 年的 6.8 亿美元成长到 2026 年的 7.7 亿美元,到 2031 年达到 14.4 亿美元,2026 年至 2031 年的复合年增长率为 13.3%。
这种快速成长与非洲大陆海底电缆部署的扩张、云端资料中心规模的扩大以及区域资料保护法律的加强直接相关。微软和G42在肯亚投资10亿美元的数位生态系统计画等超大规模资料中心业者资料中心的投资,正在将采购标准从单一解决方案转向多层云端原生安全平台(microsoft.com)。企业也面临认证专业人员长期短缺的问题——每10万人中不足2人——迫使许多企业依赖资安管理服务管治。尼日利亚的《国家资料保护法》(NDPA)和南非的《个人资讯保护法》(POPIA)等法律法规的协调统一,正迫使跨国公司将资料处理在地化,并协调跨境治理控制。同时,行动支付的普及加剧了诈骗风险,使得人工智慧驱动的生物识别和反洗钱分析在金融服务领域变得至关重要。
非洲网路安全市场趋势与洞察
撒哈拉以南非洲地区行动支付平台的快速普及
到2024年,诈欺侦测引擎发现生物识别诈骗率高达16%,是用户註册时诈欺率的四倍。这凸显了身分窃贼透过SIM卡交换和多层洗钱链窃取凭证的程度。在东非,由于身分证明文件不合格和检验系统薄弱,拒付率高达27%。仅在乌干达,预计到2024年行动支付诈骗造成的损失将达到320万美元,这将推动人工智慧驱动的异常检测工具和动态生物识别检查的广泛应用。这使得网路安全不再只是被视为合规成本,而是成为推动普惠金融成长的平台。
扩大国家资料保护条例
尼日利亚2023年《资料保护法》促使92%的受访机构在12个月内加强了安全控制,而对Meta公司处以的2.2亿美元罚款则表明监管机构愿意对违规行为处以巨额罚款。肯亚在全球网路安全指数中名列前茅,并在2025年第一季侦测到25亿次威胁,凸显了早期立法如何增强一个国家的风险应对能力(technext24.com)。这正推动跨国公司朝着统一的洲际管治框架和区域资料处理中心的方向发展。
网路安全认证人才严重短缺(每10万人不足2人)
光是尼日利亚一国到2030年就需要新增3万名专业人员,而南非高薪的中级云端安全职位年薪已超过786,648兰特(约41,400美元),推高了当地企业的成本。为了解决人员短缺问题,企业正在采用安全营运中心即服务(SOCaaS)模式和自动化技术。虽然联合国开发计画署(UNDP)和卡内基美隆大学的竞赛项目正在培养新人才,但它们每年的培训能力加起来不足2,000人,结构性的人才短缺正在减缓解决方案的推广应用。
细分市场分析
到2025年,非洲网路安全市场解决方案收入将占总收入的67.60%,而资安管理服务正以18.2%的复合年增长率快速成长,这反映出企业正显着转向外包营运。由于面临人才短缺,企业更倾向于选择综合性的SOC即服务(SOCaaS)方案,将威胁搜寻、合规性监控和事件回应整合到单一合约中。这种外包趋势有助于提升Liquid C2等区域供应商的利润率,这些供应商与超大规模资料中心业者合作,充分利用其人工智慧驱动的检测技术。同时,解决方案细分市场面临来自开放原始码替代方案的价格压力,促使供应商整合增值分析和监管工具包。
在企业应对多司法管辖区隐私法律挑战的过程中,专业服务收入在整体服务组合中成长最快。顾问公司现在将「实施+培训」模组打包,帮助客户在数月而非数年内完成从基线差距评估到审核规的转变。因此,非洲网路安全市场的支出结构正趋于整合。虽然硬体和软体授权仍然是基础要素,但基于合约的託管服务正在主导增量成长,提高了买卖双方的可预测性。
到2025年,本地部署架构将占总支出的55.10%,这反映了传统资料中心基础设施的现状;而云端采用率预计到2031年将以14.0%的复合年增长率成长。随着工作负载迁移到区域超大规模资料中心业者资料中心,新的边界定义不断涌现,使得传统防火墙难以满足需求。 TymeBank等金融服务先驱正在展示,完全云端部署的数位银行如何在满足支付卡产业资料安全标准 (PCI-DSS) 要求的同时,加快功能发布週期。因此,随着安全存取服务边际(SASE) 框架取代零散的VPN堆迭,预计到2031年,非洲云端交付控制的网路安全市场规模将超过6.5亿美元。
公共部门的工作负载仍然保持混合模式,因为资料主权条款通常要求将公民记录储存在本地。尼日利亚和埃及的本地云端营运商利用汇率波动优势,以该地货币计费,吸引那些需要可预测成本结构的政府和通讯业者租户,优于外国供应商。他们提供的捆绑式安全控制措施有效地为国内网路安全供应商带来了云端託管通路的增量收入,从而增强了本地生态系统。
其他福利:
- Excel格式的市场预测(ME)表
- 分析师支持(3个月)
目录
第一章 引言
- 研究假设和市场定义
- 调查范围
第二章调查方法
第三章执行摘要
第四章 市场情势
- 市场概览
- 市场驱动因素
- 撒哈拉以南非洲地区行动支付平台的快速普及
- 扩大国家资料保护条例(NDPR、DPA-Kenya、POPIA)
- 世界银行 DE4A 数位公共基础设施资金筹措
- 2Africa 和 Equiano 海底光缆登陆点增加频宽并扩大攻击面
- 沿岸地区油气产业的OT网路安全需求
- 超大规模资料中心业者资料中心部署推动云端原生安全
- 市场限制
- 网路安全认证人才严重短缺(每10万人不足2人)
- 传统基于SS7的通讯基础设施
- 政府采购分散且销售週期长
- 中小企业网路保险普及率低
- 关键法规结构评估
- 价值链分析
- 技术展望
- 波特五力分析
- 供应商的议价能力
- 买方的议价能力
- 新进入者的威胁
- 替代品的威胁
- 竞争对手之间的竞争
- 主要用例和案例研究
- 宏观经济因素对市场的影响
- 投资分析
第五章 市场规模与成长预测
- 报价
- 解决方案
- 应用程式安全
- 云端安全
- 资料安全
- 身分和存取管理
- 基础设施保护
- 综合风险管理
- 网路安全设备
- 端点安全
- 其他服务
- 服务
- 专业服务
- 託管服务
- 解决方案
- 透过部署模式
- 本地部署
- 云
- 按最终用户行业划分
- BFSI
- 卫生保健
- 资讯科技和电信
- 工业与国防
- 製造业
- 零售与电子商务
- 能源与公共产业
- 其他的
- 按最终用户公司规模划分
- 中小企业
- 大公司
第六章 竞争情势
- 市场集中度
- 策略趋势
- 市占率分析
- 公司简介
- Cisco Systems Inc.
- Check Point Software Technologies Ltd.
- Fortinet Inc.
- Palo Alto Networks Inc.
- IBM Corporation
- Dell Technologies(SecureWorks)
- Broadcom Inc.(Symantec)
- Trend Micro Inc.
- Sophos Group plc
- Kaspersky Lab
- Darktrace plc
- CyberArk Software Ltd.
- Dimension Data(NTT Ltd.)
- Liquid Intelligent Technologies(Liquid C2)
- BCX
- Silensec
- ESET
- Palo Alto Networks(Prisma)
- Huawei Technologies Co. Ltd.
- Oracle Corporation
第七章 市场机会与未来展望
The Africa cybersecurity market is expected to grow from USD 0.68 billion in 2025 to USD 0.77 billion in 2026 and is forecast to reach USD 1.44 billion by 2031 at 13.3% CAGR over 2026-2031.
This rapid momentum links directly to the continent's submarine-cable build-out, expanding cloud data-center footprints, and tighter regional data-protection laws. Hyperscaler investments, such as the USD 1 billion Microsoft-G42 digital-ecosystem program in Kenya, move the procurement baseline from point-solutions toward layered, cloud-native security platforms microsoft.com. Enterprises also confront a chronic shortage of certified professionals less than two experts per 100,000 population prompting many to rely on managed security service providers. Regulatory harmonization under acts such as Nigeria's NDPA and South Africa's POPIA is compelling multinational firms to localize data processing and unify governance controls across borders. Meanwhile, mobile-money adoption has heightened fraud exposure, making AI-driven biometric verification and anti-money-laundering analytics indispensable across financial services.
Africa Cybersecurity Market Trends and Insights
Rapid adoption of mobile-money platforms across SSA
Fraud-detection engines uncovered 16% biometric-fraud rates in 2024, quadruple the level at user registration, underscoring how identity-farming rings compromise credentials across SIM swaps and layered laundering chains . East Africa registers rejection rates as high as 27% due to sub-standard ID documentation and weak verification systems. Uganda alone lost USD 3.2 million to mobile-money fraud in 2024, catalyzing a surge in AI-driven anomaly-detection tools and dynamic liveness checks that reposition cybersecurity as a growth enabler for financial inclusion rather than a cost of compliance.
Expansion of national data-protection regulations
Nigeria's 2023 Data Protection Act spurred 92% of surveyed organizations to strengthen security controls within 12 months, while Meta's USD 220 million fine illustrated regulators' willingness to impose material penalties for non-compliance . Kenya's Tier 1 ranking in the Global Cybersecurity Index and the detection of 2.5 billion threats during Q1 2025 reaffirm how early statutory adoption improves national risk posture technext24.com. Multinationals are therefore pivoting to unified, continent-wide governance frameworks and localized data-processing hubs.
Severe shortage of certified cyber-security talent (< 2 pros/100 k pop.)
Nigeria alone needs 30,000 additional experts by 2030, yet premium cloud-security salaries in South Africa already exceed ZAR 786,648 (USD 41,400) for mid-level roles, inflating costs for local firms . Enterprises consequently embrace Security-Operations-Center-as-a-Service models and automation to offset human bottlenecks. Although UNDP and Carnegie Mellon competitions train new cohorts, their combined reach remains below 2,000 professionals annually, leaving a structural deficit that slows solution uptake .
Other drivers and restraints analyzed in the detailed report include:
- World Bank DE4A digital public-infrastructure funding
- Hyperscaler data-center roll-outs driving cloud-native security
- Legacy SS7-based telco infrastructure
For complete list of drivers and restraints, kindly check the Table Of Contents.
Segment Analysis
The Africa cybersecurity market recorded solutions revenue of 67.60% in 2025, yet managed-security offerings are expanding at an 18.2% CAGR, reflecting a decisive shift toward outsourced operations. Enterprises grappling with talent scarcity prefer comprehensive Security-Operations-Center-as-a-Service bundles that combine threat hunting, compliance monitoring, and incident response under single contracts. This outsourcing trend widens margins for regional providers such as Liquid C2, whose AI-infused detection stack benefits from partnerships with hyperscalers. At the same time, the solutions sub-segment faces price pressure from open-source alternatives, prompting vendors to embed value-added analytics and regulatory toolkits.
Professional-services revenue is rising fastest within the broader services mix, as firms navigate multi-jurisdictional privacy laws. Consultants now package "implementation-plus-training" modules, helping clients move from baseline gap assessments to auditable compliance in months rather than years. The Africa cybersecurity market therefore demonstrates a converging spend profile: hardware and software licenses remain foundational, but contractual managed services dominate incremental growth, improving predictability for both buyers and vendors.
On-premise architectures still captured 55.10% of 2025 spend, mirroring legacy data-center footprints, yet cloud adoption is tracking an 14.0% CAGR through 2031. Workload migration toward regional hyperscaler zones creates new perimeter definitions, rendering traditional firewalls insufficient. Financial-services pioneers such as TymeBank showcase how fully cloud-deployed digital banks can satisfy Payment Card Industry Data Security Standard (PCI-DSS) requirements while accelerating feature release cycles. Accordingly, the Africa cybersecurity market size for cloud-delivered controls is forecast to exceed USD 650 million by 2031, as secure access service edge (SASE) frameworks replace patchwork VPN stacks.
Public-sector workloads remain hybrid because data-sovereignty clauses often mandate local storage for citizen records. Local cloud operators in Nigeria and Egypt exploit currency volatility advantages over foreign providers by billing in local denominations, attracting government and telco tenants that require predictable cost structures. Their bundled security controls effectively an extension of cloud hosting channel incremental revenue toward domestic cybersecurity vendors, reinforcing regional ecosystems.
The Africa Cybersecurity Market Report Segments the Industry Into Offering (Solutions and Services), Deployment Mode (On-Premise, and Cloud), End-User Vertical (BFSI, Healthcare, IT and Telecom, Industrial and Defense, Manufacturing, Retail and E-Commerce, Energy and Utilities, and Others), and End-User Enterprise Size (SMEs, and Large Enterprises). The Market Forecasts are Provided in Terms of Value (USD).
List of Companies Covered in this Report:
- Cisco Systems Inc.
- Check Point Software Technologies Ltd.
- Fortinet Inc.
- Palo Alto Networks Inc.
- IBM Corporation
- Dell Technologies (SecureWorks)
- Broadcom Inc. (Symantec)
- Trend Micro Inc.
- Sophos Group plc
- Kaspersky Lab
- Darktrace plc
- CyberArk Software Ltd.
- Dimension Data (NTT Ltd.)
- Liquid Intelligent Technologies (Liquid C2)
- BCX
- Silensec
- ESET
- Palo Alto Networks (Prisma)
- Huawei Technologies Co. Ltd.
- Oracle Corporation
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET LANDSCAPE
- 4.1 Market Overview
- 4.2 Market Drivers
- 4.2.1 Rapid Adoption of Mobile-Money Platforms Across SSA
- 4.2.2 Expansion of National Data-Protection Regulations (NDPR, DPA-Kenya, POPIA)
- 4.2.3 World-Bank DE4A Digital Public-Infrastructure Funding
- 4.2.4 2Africa and Equiano Cable Landings Expanding Bandwidth Attack Surface
- 4.2.5 OT Cybersecurity Demand in Gulf-of-Guinea Oil and Gas
- 4.2.6 Hyperscaler Data-Center Roll-outs Driving Cloud-Native Security
- 4.3 Market Restraints
- 4.3.1 Severe Shortage of Certified Cyber-Security Talent ( <2 Pros/100k pop.)
- 4.3.2 Legacy SS7-Based Telco Infrastructure
- 4.3.3 Fragmented Government Procurement and Long Sales Cycles
- 4.3.4 Low Cyber-Insurance Penetration Among SMEs
- 4.4 Evaluation of Critical Regulatory Framework
- 4.5 Value Chain Analysis
- 4.6 Technological Outlook
- 4.7 Porter's Five Forces Analysis
- 4.7.1 Bargaining Power of Suppliers
- 4.7.2 Bargaining Power of Buyers
- 4.7.3 Threat of New Entrants
- 4.7.4 Threat of Substitutes
- 4.7.5 Competitive Rivalry
- 4.8 Key Use Cases and Case Studies
- 4.9 Impact on Macroeconomic Factors of the Market
- 4.10 Investment Analysis
5 MARKET SIZE AND GROWTH FORECASTS (VALUE)
- 5.1 By Offering
- 5.1.1 Solutions
- 5.1.1.1 Application Security
- 5.1.1.2 Cloud Security
- 5.1.1.3 Data Security
- 5.1.1.4 Identity and Access Management
- 5.1.1.5 Infrastructure Protection
- 5.1.1.6 Integrated Risk Management
- 5.1.1.7 Network Security Equipment
- 5.1.1.8 Endpoint Security
- 5.1.1.9 Other Services
- 5.1.2 Services
- 5.1.2.1 Professional Services
- 5.1.2.2 Managed Services
- 5.1.1 Solutions
- 5.2 By Deployment Mode
- 5.2.1 On-Premise
- 5.2.2 Cloud
- 5.3 By End-User Vertical
- 5.3.1 BFSI
- 5.3.2 Healthcare
- 5.3.3 IT and Telecom
- 5.3.4 Industrial and Defense
- 5.3.5 Manufacturing
- 5.3.6 Retail and E-commerce
- 5.3.7 Energy and Utilities
- 5.3.8 Others
- 5.4 By End-User Enterprise Size
- 5.4.1 Small and Medium Enterprises (SMEs)
- 5.4.2 Large Enterprises
6 COMPETITIVE LANDSCAPE
- 6.1 Market Concentration
- 6.2 Strategic Moves
- 6.3 Market Share Analysis
- 6.4 Company Profiles {(includes Global level Overview, Market level overview, Core Segments, Financials as available, Strategic Information, Market Rank/Share for key companies, Products and Services, and Recent Developments)}
- 6.4.1 Cisco Systems Inc.
- 6.4.2 Check Point Software Technologies Ltd.
- 6.4.3 Fortinet Inc.
- 6.4.4 Palo Alto Networks Inc.
- 6.4.5 IBM Corporation
- 6.4.6 Dell Technologies (SecureWorks)
- 6.4.7 Broadcom Inc. (Symantec)
- 6.4.8 Trend Micro Inc.
- 6.4.9 Sophos Group plc
- 6.4.10 Kaspersky Lab
- 6.4.11 Darktrace plc
- 6.4.12 CyberArk Software Ltd.
- 6.4.13 Dimension Data (NTT Ltd.)
- 6.4.14 Liquid Intelligent Technologies (Liquid C2)
- 6.4.15 BCX
- 6.4.16 Silensec
- 6.4.17 ESET
- 6.4.18 Palo Alto Networks (Prisma)
- 6.4.19 Huawei Technologies Co. Ltd.
- 6.4.20 Oracle Corporation
7 MARKET OPPORTUNITIES AND FUTURE OUTLOOK
- 7.1 White-space and Unmet-Need Assessment









