 |
市场调查报告书
商品编码
1630390
云端点保护:市场占有率分析、产业趋势与统计、成长预测(2025-2030)Cloud Endpoint Protection - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2025 - 2030) |
||||||
价格
※ 本网页内容可能与最新版本有所差异。详细情况请与我们联繫。
简介目录
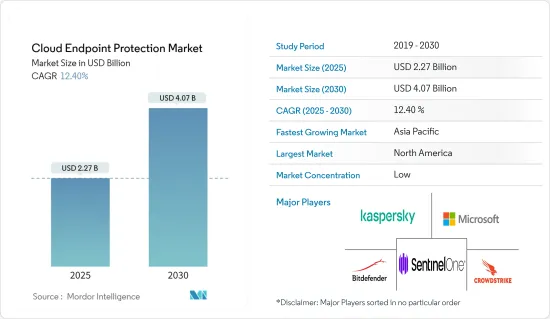
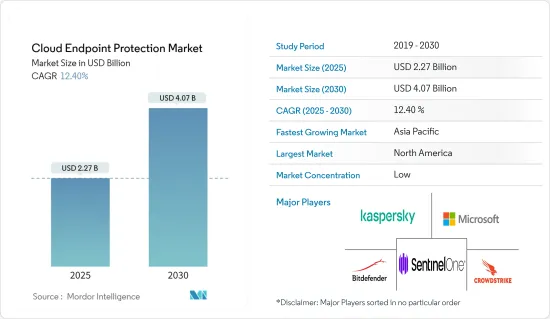
云端点保护市场规模预计到 2025 年为 22.7 亿美元,预计到 2030 年将达到 40.7 亿美元,预测期内(2025-2030 年)复合年增长率为 12.4%。
主要亮点
- 由于云端运算的日益普及以及随之而来的网路威胁的增加,云端点保护市场正在经历显着增长。这种成长也归因于各产业对云端的快速采用,这需要强而有力的安全措施。
- 远端工作和自带设备 (BYOD) 政策的激增扩大了网路犯罪分子的攻击面。从不同位置和设备存取公司资源的员工需要先进的端点保护,以防止资料外洩和其他网路威胁。基于云端的端点保护解决方案提供集中管理和即时威胁侦测,使其成为保护分散式员工的理想选择。
- 网路攻击的复杂性正在不断发展,威胁行为者正在采用先进的策略、技术和程序 (TTP)。传统的端点保护解决方案通常无法跟上这些不断变化的威胁。另一方面,基于云端的端点保护平台利用人工智慧 (AI) 和机器学习 (ML) 来即时侦测和回应威胁。这种快速适应和回应新兴威胁的能力使云端点保护成为现代网路安全策略的关键组成部分。
- 例如,2024 年 6 月,CrowdStrike 宣布与惠普企业建立策略伙伴关係,以确保端对端 AI 创新,包括 NVIDIA 加速的大规模语言模型 (LLM)。 CrowdStrike Falcon 网路安全平台、HPE GreenLake Cloud 和 OpsRamp AIOps 的整合使组织能够将 IT 营运和网路安全无缝整合到一个统一的流程中,从而安全地加速 AI 创新。
- 2024 年 5 月,以资料为中心的云端安全公司 Lookout Inc. 进行的一项新研究揭示了针对企业组织员工的行动网路钓鱼攻击的趋势。这项研究包括 250 名美国CISO 以及其他行动和云端网路安全领导者,研究发现迫切需要加强措施来应对日益增长的威胁。此外,三分之一的受访者进行了简讯网路钓鱼(33%)、社会工程(32%)、二维码网路钓鱼(30%)和语音网路钓鱼(30%)的内部模拟。
- 託管安全服务提供者(MSSP)的崛起也推动了市场成长。许多公司不具备有效管理和监控端点安全的内部专业知识。 MSSP 提供云端交付的端点保护作为其服务组合的一部分,使企业能够获得专业知识和持续监控。这一趋势使得更广泛的组织可以使用高阶端点保护,进一步推动市场成长。
- 总之,云端点保护市场的成长是由云端运算的日益普及、远端工作环境中强大的安全性需求、不断变化的网路威胁、监管合规要求、勒索软体攻击的盛行以及更广泛的安全生态推动的。
云端点保护市场趋势
医疗健康领域有望大幅成长
- 全球医疗保健产业越来越多地采用云端点保护解决方案来保护敏感资料并确保遵守严格的监管标准。有几个因素推动了这些解决方案的使用增加,包括数位病历的成长、连网医疗设备的激增以及网路威胁的日益复杂。
- 云端点保护透过云端提供即时威胁侦测、自动回应和集中管理,提供了一种全面的方法来保护笔记型电脑、智慧型手机、平板电脑和医疗设备等端点。
- 此外,在 COVID-19 大流行期间,医疗保健行业远端医疗服务的采用激增,扩大了攻击面。随着越来越多的医疗保健专业人员和患者远端存取服务,端点安全已成为重中之重。基于云端的端点保护解决方案提供了不仅限于实体位置的强大安全措施,因此远端和本地端点都受到同等保护。这对于维护远端医疗互动的完整性和保密性至关重要。
- 例如,美国主要非营利学术医疗中心梅奥诊所在整合先进网路安全措施以保护病患资料及其广泛的连网设备网路方面处于领先地位。该中心利用融合人工智慧和机器学习的云端点保护解决方案来加强其网路安全态势。这些技术使 Mayo Clinic 能够持续监控端点、侦测异常并即时回应潜在威胁。
- 2024 年 5 月,以资料为中心的云端安全公司 Lookout Inc. 宣布与领先的云端商务市场 Pax8 建立策略伙伴关係。透过这种合作关係,託管服务提供者 (MSP) 现在可以直接从 Pax8 市场购买 Lookout Mobile Endpoint Security,并由调查团队提供领先的行动资料和可操作的威胁情报作为支援。 Lookout Mobile Endpoint Security 将可见性、调查和保护相结合,为 iOS、Android 和 ChromeOS 提供业界领先的端点侦测和回应 (EDR) 解决方案。
- 医疗保健越来越多地转向云端点保护来保护患者资料。医疗保健组织管理着大量的个人识别资讯 (PII) 和受保护的健康资讯 (PHI),这使得它们很容易成为网路犯罪分子的目标。资料外洩可能会导致重大的财务损失、声誉损害和严重的法律后果。
- 云端点保护平台采用人工智慧 (AI) 和机器学习 (ML) 等先进技术来增强安全性并主动侦测和回应威胁。这些技术能够识别可能表明存在安全漏洞的异常模式和行为,从而实现快速干预和缓解。
亚太地区预计将出现显着成长
- 由于各产业持续的数位转型、网路安全威胁的增加以及云端基础方案的采用增加,亚太地区的市场正在快速成长。该地区多样化且充满活力的经济格局,加上政府的支持性政策,创造了一个有利于 CEP 解决方案扩散的环境。
- 推动亚太地区市场成长的主要因素是针对笔记型电脑、桌上型电脑和行动装置等端点的网路威胁和进阶攻击的激增。此外,银行、金融服务和保险 (BFSI)、医疗保健和零售等各个行业的快速数位化显着增加了云端中处理和储存的敏感资料量。因此,有必要实施强大的云端点保护措施,以保护资料免于外洩和未授权存取。
- 该地区不断发展的IT基础设施和高速互联网的普及进一步加速了云端点保护的采用。中国、印度、日本和韩国等国家处于这场数位革命的最前沿,它们进行了大量投资来加强互联互通和数位基础设施。随着越来越多的企业迁移到云端并需要强大的安全解决方案来保护其端点,这为市场成长奠定了坚实的基础。
- 2024 年 5 月,Amazon.com 旗下公司 Amazon Web Services (AWS) 与 CrowdStrike 宣布扩大策略伙伴关係,以加速网路安全整合和云端转型。作为伙伴关係的一部分,亚马逊将在 CrowdStrike Falcon 平台上统一其网路安全保护,从程式码到云端、从设备到资料为公司提供保护。
- 日本网路安全公司趋势科技在亚太市场站稳脚步。趋势科技提供全面的云端点保护解决方案,利用机器学习和行为分析来侦测和缓解威胁。该公司的解决方案提供持续监控、自动威胁回应以及与其他安全工具的集成,以实现端点保护的整体方法。
- 总体而言,在企业数位化程度不断提高、网路威胁激增以及云端基础的安全解决方案带来的优势的推动下,该地区的市场正在显着增长。政府监管支援、物联网的兴起以及该地区IT基础设施的改进进一步推动了这一增长。
云端点保护产业概况
云端端点保护市场高度分散,供应商规模各异,包括小型供应商、区域供应商和跨国供应商。由于激烈的市场竞争,主要企业正在专注于独特的价值提案、产品差异化、建立多种伙伴关係并扩大其地理影响力。
其他好处:
- Excel 格式的市场预测 (ME) 表
- 3 个月分析师支持
目录
第一章简介
- 研究假设和市场定义
- 调查范围
第二章调查方法
第三章执行摘要
第四章市场洞察
- 市场概况
- 产业价值链分析
- 产业吸引力-波特五力分析
- 供应商的议价能力
- 消费者议价能力
- 新进入者的威胁
- 替代品的威胁
- 竞争公司之间的敌对关係
第五章市场动态
- 市场驱动因素
- 智慧型设备的成长
- 资料外洩增加
- 市场限制因素
- 对网路攻击缺乏认识
- 评估宏观经济因素对产业的影响
第六章 市场细分
- 按公司规模
- 小型企业
- 大公司
- 依部署方式
- 私有云端
- 公共云端
- 混合云端
- 按最终用户产业
- BFSI
- 政府机构
- 卫生保健
- 能源/电力
- 零售
- 资讯科技与电信
- 其他最终用户产业
- 按地区
- 北美洲
- 欧洲
- 亚洲
- 澳洲/纽西兰
- 拉丁美洲
- 中东/非洲
第七章 竞争格局
- 公司简介
- Bitdefender LLC
- CrowdStrike Holdings, Inc.
- Microsoft Corporation
- SentinelOne Inc.
- Kaspersky Lab Inc.
- Sophos Group PLC
- Vmware, Inc.
- Cisco Systems Inc.
- McAfee LLC
- Trend Micro Inc.
- Fortinet Inc.
- Broadcom Inc.(Symantec Corporation)
- Avast Software SRO
第八章投资分析
第9章 市场的未来
简介目录
Product Code: 70497
The Cloud Endpoint Protection Market size is estimated at USD 2.27 billion in 2025, and is expected to reach USD 4.07 billion by 2030, at a CAGR of 12.4% during the forecast period (2025-2030).
Key Highlights
- The cloud endpoint protection market has experienced significant growth driven by the increased adoption of cloud computing and the corresponding rise in cyber threats. The growth can also be attributed to factors like the surge in cloud adoption across various industries, which necessitated robust security measures.
- The proliferation of remote work and bring-your-own-device (BYOD) policies expanded the attack surface for cybercriminals. Employees accessing corporate resources from various locations and devices require advanced endpoint protection to prevent data breaches and other cyber threats. Cloud endpoint protection solutions offer centralized management and real-time threat detection, making them ideal for securing a distributed workforce.
- The sophistication of cyberattacks has evolved, with threat actors employing advanced tactics, techniques, and procedures (TTPs). Traditional endpoint protection solutions often struggle to keep pace with these evolving threats. In contrast, cloud endpoint protection platforms leverage artificial intelligence (AI) and machine learning (ML) to detect and respond to threats in real time. This capability to adapt and respond to new threats quickly has made cloud endpoint protection a crucial component of modern cybersecurity strategies.
- For instance, in June 2024, CrowdStrike announced a strategic partnership with Hewlett Packard Enterprise to secure end-to-end AI innovation, including large language models (LLMs), accelerated by NVIDIA. With the integration of the CrowdStrike Falcon cybersecurity platform, HPE GreenLake cloud, and OpsRamp AIOps, organizations can seamlessly unify IT operations and cybersecurity in a single, unified process to securely accelerate AI innovation.
- In May 2024, a new survey conducted by Lookout Inc., the data-centric cloud security company, unveiled concerning trends regarding mobile phishing attacks targeting the employees of enterprise organizations. The survey, completed by 250 United States-based CISOs and other mobile and cloud cybersecurity leaders, shed light on the urgent need for enhanced measures to combat the growing threat. In addition to this, the results indicated that less than one-third of respondents conducted internal simulations of SMS phishing (33%), social engineering (32%), QR code phishing (30%), or voice phishing (30%).
- The rise of managed security service providers (MSSPs) has also bolstered the market's growth. Many organizations lack the in-house expertise to effectively manage and monitor endpoint security. MSSPs offer cloud endpoint protection as part of their service portfolio, providing organizations with access to specialized expertise and continuous monitoring. This trend has made advanced endpoint protection accessible to a broader range of organizations, further driving market growth.
- In conclusion, the growth of the cloud endpoint protection market is driven by the increasing adoption of cloud computing, the need for robust security in remote work environments, the evolution of cyber threats, regulatory compliance requirements, the prevalence of ransomware attacks, the integration with broader security ecosystems, competitive innovation, the scalability of cloud solutions, and the rise of managed security services.
Cloud Endpoint Protection Market Trends
The Healthcare Segment is Expected to Witness Significant Growth
- The global healthcare sector has been increasingly adopting cloud endpoint protection solutions to safeguard sensitive data and ensure compliance with stringent regulatory standards. The rising usage of these solutions is driven by several factors, including the increasing volume of digital patient records, the proliferation of connected medical devices, and the growing sophistication of cyber threats.
- Cloud endpoint protection offers a comprehensive approach to securing endpoints such as laptops, smartphones, tablets, and medical devices by providing real-time threat detection, automated response, and centralized management, all delivered through the cloud.
- Moreover, the healthcare sector's adoption of telehealth services, which surged during the COVID-19 pandemic, has expanded the attack surface. With more healthcare professionals and patients accessing services remotely, securing endpoints becomes paramount. Cloud endpoint protection solutions provide robust security measures that are not limited by physical location, ensuring that remote and on-premises endpoints are equally protected. This is crucial in maintaining the integrity and confidentiality of telehealth interactions.
- For instance, Mayo Clinic, a key nonprofit American academic medical center, has been at the forefront of integrating advanced cybersecurity measures to protect its extensive network of patient data and connected devices. The organization utilizes a cloud endpoint protection solution that incorporates AI and ML to enhance its cybersecurity posture. By leveraging these technologies, Mayo Clinic can continuously monitor its endpoints, detect anomalies, and respond to potential threats in real time.
- In May 2024, Lookout Inc., the data-centric cloud security company, introduced a strategic partnership with Pax8, a key cloud commerce marketplace. The partnership enables managed service providers (MSPs) to acquire Lookout Mobile Endpoint Security directly from the Pax8 Marketplace, backed by actionable threat intelligence from the leading mobile dataset and research team. Lookout Mobile Endpoint Security combines visibility, research, and protection to deliver the industry's most advanced endpoint detection and response (EDR) solution for iOS, Android, and ChromeOS.
- There is a heightened focus on cloud endpoint protection in healthcare to protect patient data. Healthcare organizations manage vast amounts of personally identifiable information (PII) and protected health information (PHI), which are prime targets for cybercriminals. Breaches can lead to significant financial losses, damage to reputation, and severe legal consequences.
- Cloud endpoint protection platforms enhance security by employing advanced technologies such as artificial intelligence (AI) and machine learning (ML) to detect and respond to threats proactively. These technologies enable the identification of unusual patterns and behaviors that may indicate a security breach, allowing for quicker intervention and mitigation.
Asia-Pacific is Expected to Witness Significant Growth
- Asia-Pacific is witnessing rapid growth in the market, driven by increasing digital transformation across industries, rising cybersecurity threats, and the increasing adoption of cloud-based solutions. The region's diverse and dynamic economic landscape, coupled with supportive government policies, is fostering a conducive environment for the proliferation of CEP solutions.
- The primary factors contributing to the growth of the market in Asia-Pacific are the surge in cyber threats and sophisticated attacks targeting endpoints, including laptops, desktops, and mobile devices. Furthermore, the rapid digitization of various sectors, such as banking, financial services, and insurance (BFSI), healthcare, and retail, has significantly increased the volume of sensitive data being processed and stored in the cloud. This has necessitated the deployment of robust cloud endpoint protection measures to safeguard data against breaches and unauthorized access.
- The region's growing IT infrastructure and the increasing penetration of high-speed internet are further fueling the adoption of cloud endpoint protection. Countries like China, India, Japan, and South Korea are at the forefront of this digital revolution, with substantial investments being made in enhancing connectivity and digital infrastructure. This is providing a solid foundation for the growth of the market as more businesses migrate to the cloud, requiring robust security solutions to protect endpoints.
- In May 2024, Amazon Web Services (AWS), an Amazon.com company, and CrowdStrike announced an expanded strategic partnership to accelerate cybersecurity consolidation and cloud transformation. As part of the partnership, Amazon unified its cybersecurity protection on the CrowdStrike Falcon platform, protecting the company from code to cloud and device to data.
- Trend Micro, a Japanese cybersecurity company, has a strong foothold in the Asia-Pacific market. Trend Micro offers a comprehensive cloud endpoint protection solution that leverages machine learning and behavioral analysis to detect and mitigate threats. The company's solution provides continuous monitoring, automated threat response, and integration with other security tools to offer a holistic approach to endpoint protection.
- Overall, the region is experiencing significant market growth, driven by the increasing digitalization of businesses, the surge in cyber threats, and the advantages offered by cloud-based security solutions. The support from government regulations, the rise of IoT, and the region's improving IT infrastructure are further propelling this growth.
Cloud Endpoint Protection Industry Overview
The cloud endpoint protection market is highly fragmented due to several vendors across all scales, i.e., small-scale, regional, and large multi-national scales. Due to intense market rivalry, key players focus on making unique value prepositions, product differentiation, and forming multiple partnerships to increase their geographical presence.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET INSIGHTS
- 4.1 Market Overview
- 4.2 Industry Value Chain Analysis
- 4.3 Industry Attractiveness - Porter's Five Forces Analysis
- 4.3.1 Bargaining Power of Suppliers
- 4.3.2 Bargaining Power of Consumers
- 4.3.3 Threat of New Entrants
- 4.3.4 Threat of Substitutes
- 4.3.5 Intensity of Competitive Rivalry
5 MARKET DYNAMICS
- 5.1 Market Drivers
- 5.1.1 Growth of Smart Devices
- 5.1.2 Increasing number of Data Breaches
- 5.2 Market Restraints
- 5.2.1 Lack of Awareness about Cyberattacks
- 5.3 Assessment of Impact of Macroeconomic Factors on the Industry
6 MARKET SEGMENTATION
- 6.1 By Enterprise Size
- 6.1.1 Small & Medium Enterprises
- 6.1.2 Large Enterprises
- 6.2 By Deployment Mode
- 6.2.1 Private Cloud
- 6.2.2 Public Cloud
- 6.2.3 Hybrid Cloud
- 6.3 By End-user Industry
- 6.3.1 BFSI
- 6.3.2 Government
- 6.3.3 Healthcare
- 6.3.4 Energy and Power
- 6.3.5 Retail
- 6.3.6 IT & Telecom
- 6.3.7 Other End-user Industry
- 6.4 By Geography
- 6.4.1 North America
- 6.4.2 Europe
- 6.4.3 Asia
- 6.4.4 Australia and New Zealand
- 6.4.5 Latin America
- 6.4.6 Middle East and Africa
7 COMPETITIVE LANDSCAPE
- 7.1 Company Profiles
- 7.1.1 Bitdefender LLC
- 7.1.2 CrowdStrike Holdings, Inc.
- 7.1.3 Microsoft Corporation
- 7.1.4 SentinelOne Inc.
- 7.1.5 Kaspersky Lab Inc.
- 7.1.6 Sophos Group PLC
- 7.1.7 Vmware, Inc.
- 7.1.8 Cisco Systems Inc.
- 7.1.9 McAfee LLC
- 7.1.10 Trend Micro Inc.
- 7.1.11 Fortinet Inc.
- 7.1.12 Broadcom Inc. (Symantec Corporation)
- 7.1.13 Avast Software SRO
8 INVESTMENT ANALYSIS
9 FUTURE OF THE MARKET
02-2729-4219
+886-2-2729-4219










