 |
市场调查报告书
商品编码
1939643
DDoS攻击缓解:市场占有率分析、产业趋势与统计、成长预测(2026-2031年)Distributed Denial Of Service (DDoS) Protection - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2026 - 2031) |
||||||
※ 本网页内容可能与最新版本有所差异。详细情况请与我们联繫。
据估计,DDoS 防护市场规模将从 2025 年的 47.3 亿美元成长到 2026 年的 53.8 亿美元。
预计到 2031 年将达到 102.8 亿美元,2026 年至 2031 年的复合年增长率为 13.82%。
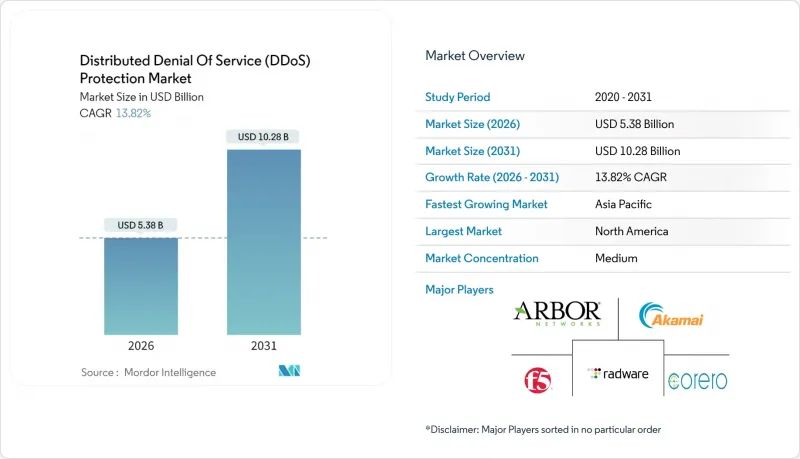
此次扩张的驱动因素包括多向量Terabit特级安全事件的日益频繁、监管要求的不断加强以及混合和云端缓解模式的普及。以解决方案为中心的产品将在2024年保持61.23%的市场份额,这印证了企业对整合式可程式防御系统的需求。云端优先部署占据了近一半的潜在市场,但随着企业在延迟、控制和合规性之间寻求平衡,混合架构正在迅速崛起。区域趋势依然重要,北美地区将继续保持领先地位,预计2024年将占据39.34%的收入份额,而亚太地区则凭藉5G的快速部署和物联网的蓬勃发展,以14.89%的复合年增长率增长。
全球DDoS攻击缓解市场趋势及洞察
多向量攻击的频率日益增加
有史以来规模最大的攻击事件发生在2025年,流量高达6.3Tbps,这凸显了攻击方式从简单的流量型攻击向复杂的通讯协定和应用层攻击的转变,这种转变使传统的基于规则的设备不堪重负,并加速了自适应人工智慧驱动平台的普及。通讯服务供应商和金融机构仍然是高价值的攻击目标,世界各地的监管机构都要求关键基础设施营运商证明其具备强大的韧性。
快速转向云端和混合响应模式
短期突发性攻击的兴起,使得弹性持久的云端安全防护至关重要。然而,对延迟敏感的工作负载仍需要本地部署的安全防御,从而推动了混合云环境的需求。超大规模云端与专业安全公司合作,帮助中小企业满足新的合规要求,同时弥补技能差距。
中小企业自有设备整体拥有成本高昂
资本密集硬体和持续的签章更新仍然是中小企业面临的障碍,因此需要订阅式云端清洗和託管 SOC 服务相结合的方式。
细分市场分析
到2025年,解决方案领域将占总收入的60.65%,因为越来越多的组织寻求整合式、可程式设计的防御方案,以应对从L3/4层流量攻击到L7层应用程式泛光利用等各种威胁。虽然网路层防护仍将占据该领域最大份额,但由于能够模仿合法用户行为的AI驱动型机器人的兴起,高级机器人防护领域预计将以15.05%的复合年增长率增长。供应商正在整合机器学习分类器、设备指纹识别和即时挑战机制,以抵御人员编制和凭证囤积攻击。随着供应商整合,託管服务和专业服务在合规报告和全天候监控方面的重要性日益凸显。解决方案和服务之间的相互作用凸显了DDoS防护市场转向基于结果的合约模式的趋势。
混合配置的日益普及要求本地设备、云端流量净化中心和容器化网路功能之间进行协作。随着产品功能的融合,差异化优势正转向以 API 为中心的整合、攻击取证深度和零信任支援。能够将行为分析与可操作情报结合的供应商,将更有利于利用监管机构日益增长的压力,在关键领域展现出可验证的韧性。
2025年,基于云端的防御方案将占据DDoS防护市场规模的49.02%,利用弹性频宽池和全球任播路由技术,能够抵御每秒数太比特的攻击。全天候运作模式可确保秒级回应,这在当今频繁出现的亚分钟级「脉衝式」攻击中至关重要。同时,混合架构到2031年将以15.25%的复合年增长率成长,企业将低延迟的本地检测与云端规模的流量清洗相结合,以应对流量高峰。这种灵活的方法既能最大限度地降低资本支出和营运复杂性,又能满足各司法管辖区的数据限制。
本地部署设备在金融交易平台、国防机构和需要微秒响应的媒体广播公司中仍占有一席之地。然而,即使是这些垂直行业也越来越多地采用分层云端容量来应对高流量溢出。在站点、筛检节点和 SIEM 平台之间持续进行 API 驱动的遥测资料交换正成为 DDoS 防护市场的一项基本要求。
DDoS攻击缓解市场报告按组件(解决方案、服务)、部署类型(云端、本地部署、混合部署)、组织规模(中小企业、大型企业)、最终用户产业(政府与国防、银行、金融服务与保险、其他)以及地区进行细分。市场预测以美元计价。
区域分析
北美39.05%的市占率凸显了其成熟但又动盪的市场环境。金融、SaaS和能源产业是高价值目标。网路安全和基础设施安全局 (CISA) 的指南日益要求即时遥测资料共用和零信任实践,从而推动供应商和客户在事件回应方面进行更深入的合作。投资重点在于加密流量侦测和机器学习驱动的异常评分。
亚太地区以14.65%的复合年增长率展现出最强劲的成长动能。数位经济每年新增数千万宽频和行动用户,扩大了殭尸网路的招募潜力。该地区的通讯业者正与安全厂商合作,在其5G核心网路中部署边缘清洗节点,以降低跳数延迟并改善用户体验。日本和澳洲的监管机构现已要求关键基础设施营运商提交季度弹性报告,这进一步提振了对DDoS防护市场的整体需求。
在欧洲,如何在严格的隐私法规和日益复杂的网路攻击之间取得平衡是一项挑战。 NIS2 指示规定,对于防御措施不足的企业,将处以最高相当于全球营业额 2% 的罚款,这加速了企业向经认证的多租户防御服务的转型。中欧和东欧的公共产业面临着出于政治动机的泛光攻击,这促使它们采用基于人工智慧的流量分类和主权资料託管保障相结合的技术。拉丁美洲、中东和非洲正在成为殭尸网路和定向攻击的新来源地,因此,DDoS 防护市场需要製定能够考虑区域特征的、情境感知型的防御策略。
其他福利:
- Excel格式的市场预测(ME)表
- 分析师支持(3个月)
目录
第一章 引言
- 研究假设和市场定义
- 调查范围
第二章调查方法
第三章执行摘要
第四章 市场情势
- 市场概览
- 市场驱动因素
- 多向量太比Terabit攻击频率不断增加
- 快速过渡到云端和混合缓解模式
- 物联网、5G 和边缘连接设备的兴起
- 人工智慧驱动的「DDoS即服务」市场降低了进入门槛
- 关键基础设施法规强制要求具备韧性(例如,NIS2、CISA)
- 在网路边缘部署基于SDN的可程式清洗机制
- 市场限制
- 中小企业自备设备高成本
- 网路安全专业人员短缺
- 由于加密攻击流量比例不断增加,可见性受到限制。
- 误报导致自身系统停机的风险
- 监管环境
- 技术展望
- 波特五力分析
- 新进入者的威胁
- 买方的议价能力
- 供应商的议价能力
- 替代品的威胁
- 竞争对手之间的竞争
- 用例和案例研究
第五章 市场规模与成长预测
- 按组件
- 解决方案
- 网路层保护
- 应用层保护
- DNS保护
- 高阶机器人防护
- 服务
- 专业服务
- 託管服务
- 解决方案
- 透过部署模式
- 云
- 本地部署
- 杂交种
- 按组织规模
- 小型企业
- 大公司
- 按最终用户行业划分
- 政府和国防部
- 银行、金融服务和保险
- 资讯科技与通讯
- 医疗保健和生命科学
- 零售与电子商务
- 媒体与娱乐
- 能源与公共产业
- 製造业
- 其他终端用户产业
- 按地区
- 北美洲
- 我们
- 加拿大
- 墨西哥
- 南美洲
- 巴西
- 阿根廷
- 南美洲其他地区
- 欧洲
- 英国
- 德国
- 法国
- 义大利
- 西班牙
- 俄罗斯
- 其他欧洲地区
- 亚太地区
- 中国
- 日本
- 印度
- 韩国
- 澳洲和纽西兰
- 亚太其他地区
- 中东和非洲
- 中东
- 沙乌地阿拉伯
- 阿拉伯聯合大公国
- 土耳其
- 其他中东地区
- 非洲
- 南非
- 奈及利亚
- 其他非洲地区
- 中东
- 北美洲
第六章 竞争情势
- 市场集中度
- 策略趋势
- 市占率分析
- 公司简介
- NETSCOUT Systems, Inc.
- Akamai Technologies, Inc.
- F5, Inc.
- Imperva, Inc.
- Radware Ltd.
- Corero Network Security plc
- Neustar, Inc.
- Cloudflare, Inc.
- Nexusguard Limited
- DOSarrest Internet Security Limited
- VeriSign, Inc.
- Amazon Web Services, Inc.
- Microsoft Corporation
- Google LLC
- Check Point Software Technologies Ltd.
- Fortinet, Inc.
- A10 Networks, Inc.
- Fastly, Inc.
- Alibaba Cloud Computing Co., Ltd.
- StackPath, LLC
- GCore Labs SA
- Link11 GmbH
- Lumen Technologies, Inc.
- Sucuri, Inc.
第七章 市场机会与未来展望
DDoS protection market size in 2026 is estimated at USD 5.38 billion, growing from 2025 value of USD 4.73 billion with 2031 projections showing USD 10.28 billion, growing at 13.82% CAGR over 2026-2031.
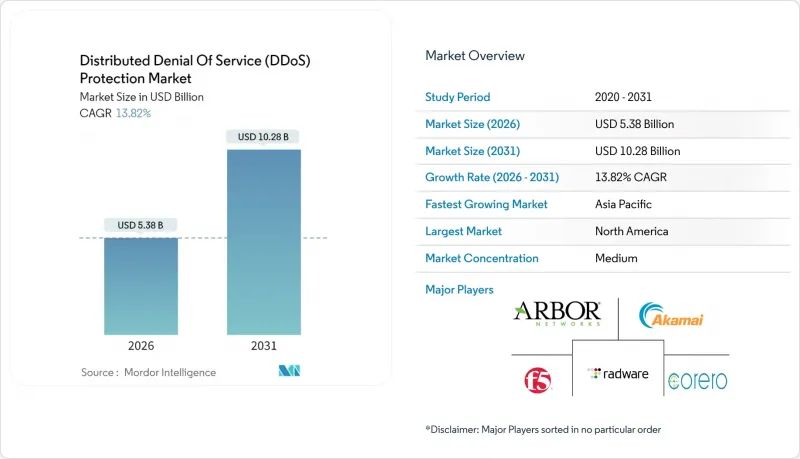
This expansion is fueled by the mounting frequency of multi-vector, terabit-scale incidents, strengthened regulatory mandates, and the widespread embrace of hybrid and cloud-based mitigation models. Solution-centric offerings maintained dominance with 61.23% share in 2024, underscoring enterprise demand for integrated, programmable defenses. Cloud-first deployments accounted for nearly half the addressable opportunity, yet hybrid architectures are gaining ground as organizations balance latency, control, and compliance. Regional dynamics remain pivotal: North America led with 39.34% revenue share in 2024, while Asia Pacific is advancing at a 14.89% CAGR, driven by rapid 5G rollouts and surging IoT adoption.
Global Distributed Denial Of Service (DDoS) Protection Market Trends and Insights
Escalating frequency of multi-vector attacks
A record 6.3 Tbps event in 2025 highlighted the jump from volumetric floods to blended protocol and application-layer campaigns, overwhelming legacy rule-based appliances and escalating procurement of adaptive, AI-driven platforms. Communication service providers and financial institutions remain high-value targets, and global regulators now require demonstrated resilience for critical infrastructure operators.
Rapid migration to cloud and hybrid mitigation models
Elastic, always-on cloud scrubbing has become indispensable as short-burst attacks spike; however, latency-sensitive workloads keep on-premises defenses relevant, accelerating hybrid demand. Partnerships between hyperscale clouds and security specialists are bridging skills gaps for SMEs while meeting emerging compliance obligations.
High TCO of on-prem appliances for SMEs
Capex-heavy hardware plus ongoing signature updates remain prohibitive for smaller enterprises, steering demand toward subscription-based cloud scrubbing paired with managed SOC services.
Other drivers and restraints analyzed in the detailed report include:
- Expansion of IoT-, 5G-, and edge-connected devices
- AI-powered "DDoS-as-a-Service" marketplaces lowering entry barriers
- Shortage of skilled cybersecurity professionals
For complete list of drivers and restraints, kindly check the Table Of Contents.
Segment Analysis
Solutions commanded 60.65% revenue in 2025 as enterprises sought unified, programmable defenses capable of spanning L3/4 volumetric floods and L7 application abuses. Within this umbrella, network-layer protection retained the largest slice, yet advanced bot mitigation is forecast to rise at a 15.05% CAGR, driven by AI-enabled bots that mimic legitimate user behavior. Vendors are embedding machine-learning classifiers, device fingerprinting, and real-time challenge mechanisms to blunt credential-stuffing and inventory hoarding. Services-managed and professional-continue to gain relevance as organizations consolidate suppliers for compliance reporting and 24X7 monitoring. The interplay of solutions and services underscores a shift toward outcome-based contracting across the DDoS protection market.
Growing adoption of hybrid topologies demands orchestration between on-premises hardware, cloud scrubbing centers, and containerized network functions. As offerings converge, differentiation pivots on API-centric integration, attack-forensics depth, and zero-trust alignment. Solution vendors that blend behavioral analytics with actionable intelligence are positioned to capitalize on rising regulatory pressure for demonstrable resiliency across critical sectors.
Cloud-based defenses captured 49.02% of the DDoS protection market size in 2025, offering elastic bandwidth pools and global anycast routing to absorb multi-Tbps assaults. Always-on models ensure response within seconds, a necessity amid sub-minute "pulse" attacks. Meanwhile, hybrid architectures are projected to expand at a 15.25% CAGR through 2031 as enterprises merge low-latency, on-premises detection with cloud-scale scrubbing during surge periods. This flexible posture satisfies jurisdictional data constraints while minimizing capex and operational complexity.
On-premises appliances retain niche traction among financial trading platforms, defense agencies, and media broadcasters that demand micro-second mitigation. However, even these verticals are layering cloud capacity for volumetric overflow. Continuous API-driven telemetry exchange between sites, scrubbing nodes, and SIEM platforms is becoming table stakes across the DDoS protection market.
The Distributed Denial of Service (DDoS) Protection Market Report is Segmented by Component (Solutions, and Services), Deployment Mode (Cloud, On-Premises, and Hybrid), Organization Size (Small and Medium Enterprises, and Large Enterprises), End-User Industry (Government and Defense, Banking, Financial Services and Insurance, and More), and Geography. The Market Forecasts are Provided in Terms of Value (USD),
Geography Analysis
North America's 39.05% share underscores a mature yet volatile landscape. High-value targets include finance, SaaS, and energy. CISA directives increasingly require real-time telemetry sharing and zero-trust alignment, prompting deeper vendor-customer collaboration on incident response. Investments prioritize encrypted-traffic inspection and machine-learning-driven anomaly scoring.
Asia Pacific exhibits the strongest growth trajectory at 14.65% CAGR. Digital economies are onboarding tens of millions of new broadband and mobile subscribers annually, amplifying botnet recruitment potential. Regional telcos partner with security vendors to deploy edge scrubbing nodes across 5G core networks, reducing hop latency and improving customer experience. Regulatory agencies in Japan and Australia now mandate quarterly resilience reporting for critical infrastructure operators, reinforcing demand across the DDoS protection market.
Europe balances stringent privacy mandates with elevated attack sophistication. NIS2 imposes fines up to 2% of global turnover for inadequate defenses, accelerating migration toward certified, multi-tenant mitigation services. Central and Eastern European utilities face politically motivated flood attacks, driving adoption of AI-guided traffic classification coupled with sovereign data-hosting guarantees. Latin America, the Middle East, and Africa represent emerging vectors both for botnet origination and targeted campaigns, necessitating localized, context-aware defense strategies within the DDoS protection market.
- NETSCOUT Systems, Inc.
- Akamai Technologies, Inc.
- F5, Inc.
- Imperva, Inc.
- Radware Ltd.
- Corero Network Security plc
- Neustar, Inc.
- Cloudflare, Inc.
- Nexusguard Limited
- DOSarrest Internet Security Limited
- VeriSign, Inc.
- Amazon Web Services, Inc.
- Microsoft Corporation
- Google LLC
- Check Point Software Technologies Ltd.
- Fortinet, Inc.
- A10 Networks, Inc.
- Fastly, Inc.
- Alibaba Cloud Computing Co., Ltd.
- StackPath, LLC
- GCore Labs S.A.
- Link11 GmbH
- Lumen Technologies, Inc.
- Sucuri, Inc.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions and Market Definition
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET LANDSCAPE
- 4.1 Market Overview
- 4.2 Market Drivers
- 4.2.1 Escalating frequency of multi-vector, terabit-scale attacks
- 4.2.2 Rapid migration to cloud and hybrid mitigation models
- 4.2.3 Expansion of IoT-, 5G- and edge-connected devices
- 4.2.4 AI-powered "DDoS-as-a-Service" marketplaces lowering entry barriers
- 4.2.5 Critical-infrastructure regulations mandating resiliency (e.g., NIS2, CISA)
- 4.2.6 Adoption of programmable SDN-based scrubbing at the network edge
- 4.3 Market Restraints
- 4.3.1 High TCO of on-prem appliances for SMEs
- 4.3.2 Shortage of skilled cyber-security professionals
- 4.3.3 Rising share of encrypted attack traffic limiting visibility
- 4.3.4 Risk of false-positive mitigation causing self-inflicted downtime
- 4.4 Regulatory Landscape
- 4.5 Technological Outlook
- 4.6 Porter's Five Forces Analysis
- 4.6.1 Threat of New Entrants
- 4.6.2 Bargaining Power of Buyers
- 4.6.3 Bargaining Power of Suppliers
- 4.6.4 Threat of Substitutes
- 4.6.5 Intensity of Competitive Rivalry
- 4.7 Use Case and Case Studies
5 MARKET SIZE AND GROWTH FORECASTS (VALUE)
- 5.1 By Component
- 5.1.1 Solution
- 5.1.1.1 Network-layer protection
- 5.1.1.2 Application-layer protection
- 5.1.1.3 DNS protection
- 5.1.1.4 Advanced bot mitigation
- 5.1.2 Service
- 5.1.2.1 Professional services
- 5.1.2.2 Managed services
- 5.1.1 Solution
- 5.2 By Deployment Mode
- 5.2.1 Cloud
- 5.2.2 On-Premises
- 5.2.3 Hybrid
- 5.3 By Organization Size
- 5.3.1 Small and Medium Enterprises
- 5.3.2 Large Enterprises
- 5.4 By End-User Industry
- 5.4.1 Government and Defense
- 5.4.2 Banking, Financial Services and Insurance
- 5.4.3 Information Technology and Telecommunications
- 5.4.4 Healthcare and Life Sciences
- 5.4.5 Retail and E-commerce
- 5.4.6 Media and Entertainment
- 5.4.7 Energy and Utilities
- 5.4.8 Manufacturing
- 5.4.9 Other End-User Industries
- 5.5 By Geography
- 5.5.1 North America
- 5.5.1.1 United States
- 5.5.1.2 Canada
- 5.5.1.3 Mexico
- 5.5.2 South America
- 5.5.2.1 Brazil
- 5.5.2.2 Argentina
- 5.5.2.3 Rest of South America
- 5.5.3 Europe
- 5.5.3.1 United Kingdom
- 5.5.3.2 Germany
- 5.5.3.3 France
- 5.5.3.4 Italy
- 5.5.3.5 Spain
- 5.5.3.6 Russia
- 5.5.3.7 Rest of Europe
- 5.5.4 Asia Pacific
- 5.5.4.1 China
- 5.5.4.2 Japan
- 5.5.4.3 India
- 5.5.4.4 South Korea
- 5.5.4.5 Australia and New Zealand
- 5.5.4.6 Rest of Asia Pacific
- 5.5.5 Middle East and Africa
- 5.5.5.1 Middle East
- 5.5.5.1.1 Saudi Arabia
- 5.5.5.1.2 United Arab Emirates
- 5.5.5.1.3 Turkey
- 5.5.5.1.4 Rest of Middle East
- 5.5.5.2 Africa
- 5.5.5.2.1 South Africa
- 5.5.5.2.2 Nigeria
- 5.5.5.2.3 Rest of Africa
- 5.5.5.1 Middle East
- 5.5.1 North America
6 COMPETITIVE LANDSCAPE
- 6.1 Market Concentration
- 6.2 Strategic Moves
- 6.3 Market Share Analysis
- 6.4 Company Profiles (includes Global-level Overview, Market-level Overview, Core Segments, Financials, Strategic Information, Market Rank/Share, Products and Services, Recent Developments)
- 6.4.1 NETSCOUT Systems, Inc.
- 6.4.2 Akamai Technologies, Inc.
- 6.4.3 F5, Inc.
- 6.4.4 Imperva, Inc.
- 6.4.5 Radware Ltd.
- 6.4.6 Corero Network Security plc
- 6.4.7 Neustar, Inc.
- 6.4.8 Cloudflare, Inc.
- 6.4.9 Nexusguard Limited
- 6.4.10 DOSarrest Internet Security Limited
- 6.4.11 VeriSign, Inc.
- 6.4.12 Amazon Web Services, Inc.
- 6.4.13 Microsoft Corporation
- 6.4.14 Google LLC
- 6.4.15 Check Point Software Technologies Ltd.
- 6.4.16 Fortinet, Inc.
- 6.4.17 A10 Networks, Inc.
- 6.4.18 Fastly, Inc.
- 6.4.19 Alibaba Cloud Computing Co., Ltd.
- 6.4.20 StackPath, LLC
- 6.4.21 GCore Labs S.A.
- 6.4.22 Link11 GmbH
- 6.4.23 Lumen Technologies, Inc.
- 6.4.24 Sucuri, Inc.
7 MARKET OPPORTUNITIES AND FUTURE OUTLOOK
- 7.1 White-space and Unmet-need Assessment












