 |
市场调查报告书
商品编码
1993567
全球安全测试市场:按类型、网路安全测试、应用测试工具划分-预测(至 2031 年)Security Testing Market by Type (Network, Application, Device, Social Engineering), Network Security Testing (Penetration Testing, Vulnerability Scanning, Firewall), Application Testing Tool (RASP, SAST, DAST, IAST) - Global Forecast to 2031 |
||||||
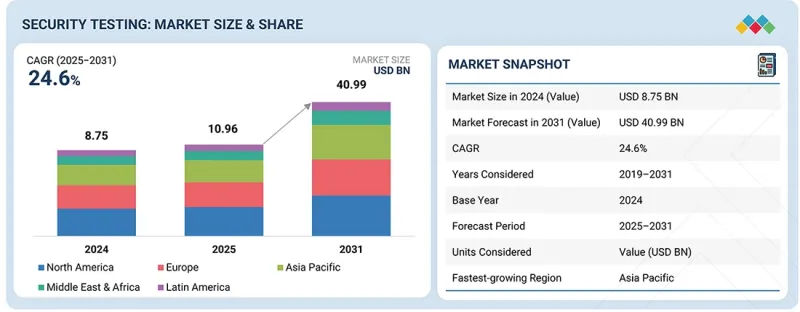
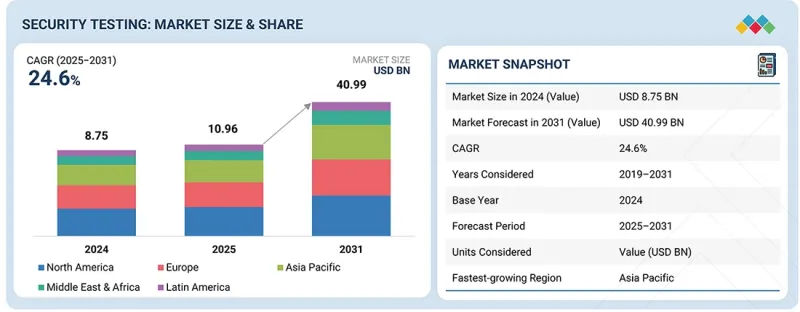
全球安全测试市场预计将从 2025 年的 109.6 亿美元成长到 2031 年的 409.9 亿美元,预测期内复合年增长率为 24.6%。
| 调查范围 | |
|---|---|
| 调查期 | 2019-2031 |
| 基准年 | 2024 |
| 预测期 | 2025-2031 |
| 单元 | 10亿美元 |
| 部分 | 安全测试类型、网路安全测试类型、应用程式安全测试类型、应用安全测试工具、部署方法、组织规模、产业、地区 |
| 目标区域 | 北美洲、欧洲、亚太地区、中东和非洲、拉丁美洲 |
这一市场的发展动力源自于网路和行动应用的快速普及。这导致暴露于外部世界的数位介面数量显着增加,使其更容易遭受网路攻击。此外,企业被迫在不影响使用者体验的前提下频繁发布更新和新功能。发布週期的加速增加了安全漏洞出现的风险,因此,定期且系统化的安全测试对于维护应用程式的可靠性、效能和使用者信任,同时保持业务敏捷性至关重要。
“按应用安全测试类型划分,预计行动应用安全测试领域在预测期内将实现最高的复合年增长率。”
随着企业越来越依赖行动应用进行客户服务、支付和员工支持,行动应用安全测试正经历最快的成长。行动应用通常在各种装置和作业系统上运行,处理敏感的个人和财务数据,这增加了暴露于安全漏洞的风险。根据 Veracode 统计,截至 2025 年 1 月,企业评估的行动应用经常出现身分验证和资料处理的缺陷,反映出快速开发週期造成的持续性安全漏洞。此外,由于行动应用经常更新以支援新功能,因此可能影响效能和用户信任的漏洞风险更高。
自带设备办公室 (BYOD) 政策和远端办公模式的日益普及,使得整个企业环境面临行动威胁的风险不断增加。安全测试对于检验安全的编码实践、API 整合以及支援行动应用程式的后端整合至关重要。行动应用程式安全测试能够帮助企业在部署前识别漏洞、保护用户资料并维护应用程式的可靠性。随着行动平台在银行、金融和保险 (BFSI)、零售、医疗保健和政府等行业的数位化管道中扮演着越来越重要的角色,对专业行动安全测试的需求也在持续增长。
“按网路安全类型划分,预计到 2025 年,网路渗透测试领域将占据最大的市场份额。”
网路渗透测试占据最大的市场份额,因为它能够模拟真实的攻击场景并检验安全措施的有效性。企业经营复杂的网路环境,涵盖本地基础设施、云端平台和远端存取系统。 Rapid7 预测,到 2025 年 2 月,企业将越来越依赖穿透测试来识别自动化扫描无法侦测到的漏洞,例如配置错误和横向移动路径。这种洞察力对于了解攻击者如何利用网路弱点至关重要。
本报告对全球安全测试市场进行了深入分析,深入探讨了关键驱动因素和限制因素、产品开发和创新以及竞争格局。
目录
第一章:引言
第二章执行摘要
第三章 主要发现
- 安全测试市场对企业而言极具吸引力的机会
- 安全测试市场:依安全测试类型划分
- 网路安全测试市场:按网路安全测试类型划分
- 安全测试市场:按应用安全测试类型划分
- 安全测试市场:按应用安全测试工具划分
- 安全测试市场:按产业划分
- 安全测试市场:按地区划分
第四章 市场概览
- 市场动态
- 促进因素
- 抑制因子
- 机会
- 任务
- 未满足的需求和閒置频段
- 相互关联的市场与跨产业机会
- 互联市场
- 跨部门机会
- 一级/二级/三级公司的策略性倡议
- 跨层战略模式
- 策略趋势
第五章 产业趋势
- 波特五力分析
- 总体经济指标
- GDP趋势与预测
- 全球资讯与通讯科技产业趋势
- 全球网路安全产业趋势
- 价值链分析
- 安全测试工具和服务供应商
- 技术提供者
- 顾问和整合商
- 监管机构和标准
- 加值经销商/经销商/经销商
- 最终用户
- 生态系统
- 定价分析
- 主要企业平均售价趋势:依测试类型划分
- 参考价格分析:依供应商划分
- 2026年将举办的主要会议和活动
- 影响客户业务的趋势与干扰因素
- 投资和资金筹措场景
- 案例研究分析
- 2025年美国关税的影响-安全测试市场
- 主要关税税率
- 价格影响分析
- 国家/地区
- 对终端用户产业的影响
第六章:技术进步、人工智慧的影响、专利、创新与未来应用
- 技术分析
- 主要新技术
- 互补技术
- 邻近技术
- 技术蓝图
- 短期 | 基础建设与初步商业化(2026-2027 年)
- 中期规划:扩大规模、资讯化与生态系扩展(2027-2030年)
- 长期 | 自主、即时、自适应安全(2030-2035 年及以后)
- 专利分析
- 未来用途
- 自主式、人工智慧驱动的安全测试平台
- 资料驱动的安全分析与预测风险洞察
- 进阶威胁模拟与攻击模拟
- 人工智慧驱动的自适应安全测试和风险优先排序
- 持续安全检验和DevSecOps整合测试
- 人工智慧/生成式人工智慧对安全测试市场的影响
- 安全测试市场的最佳实践
- 人工智慧在安全测试市场应用案例研究研究
- 相互关联的邻近生态系及其对市场参与企业的影响
- 客户在安全测试市场采用生成式人工智慧的准备情况
- 成功案例和实际应用
- CHECKMARX:变革全球企业安全软体开发
- RAPID7:全球企业的云端原生漏洞管理解决方案
第七章 监理情势
- 当地法规和合规性
- 监管机构、政府机构和其他组织
- 业界标准
第八章 消费者趋势与购买行为
- 决策流程
- 买方相关利益者和采购评估标准
- 采购过程中的关键相关利益者
- 购买标准
- 招募障碍和内部挑战
- 各个终端用户产业中尚未满足的需求
- 市场盈利
- 潜在收入
- 成本趋势
- 提高关键应用领域利润率的机会
第九章:安全测试市场:依安全测试类型划分
- 网路安全测试
- 应用程式安全测试
- 设备安全测试
- 社交工程测试
第十章 安全测试市场:依网路安全测试类型划分
- 网路渗透测试
- 漏洞扫描
- Wi-Fi/无线安全测试
- 防火墙安全测试
- 网路设定审核
第十一章 安全测试市场:依应用程式安全测试类型划分
- 行动应用安全测试
- Web应用程式安全性测试
- API 安全测试
- 安全代码审查
第十二章 安全测试市场:依应用安全测试工具划分
- RASP
- SAST
- DAST
- IAST
第十三章:安全测试市场:依部署方式划分
- 现场
- 云
第十四章:安全测试市场:依组织规模划分
- 大公司
- 小型企业
第十五章 安全测试市场:依产业划分
- BFSI
- 医疗保健
- 政府/国防
- 资讯科技/ITeS
- 沟通
- 製造业
- 零售与电子商务
- 教育
- 能源与公共产业
- 其他行业
第十六章:安全测试市场:按地区划分
- 北美洲
- 北美安全测试市场驱动因素
- 我们
- 加拿大
- 欧洲
- 欧洲安全测试市场的驱动因素
- 英国
- 德国
- 法国
- 义大利
- 其他欧洲国家
- 亚太地区
- 亚太地区安全测试市场驱动因素
- 中国
- 日本
- 印度
- 亚太其他地区
- 中东和非洲
- 中东和非洲安全测试市场的驱动因素
- GCC
- 南非
- 其他中东和非洲
- 拉丁美洲
- 拉丁美洲安全测试市场的驱动因素
- 巴西
- 墨西哥
- 其他拉丁美洲
第十七章 竞争格局
- 主要参与企业的策略/优势(2024-2026 年)
- 收入分析(2020-2024)
- 市占率分析(2025 年)
- 品牌对比
- 企业评估矩阵:主要企业(2025 年)
- 公司评估矩阵:Start-Ups/中小企业(2025 年)
- 企业评估与财务指标
- 竞争格局与趋势
第十八章:公司简介
- 主要企业
- IBM
- OPENTEXT
- CIGNITI TECHNOLOGIES
- INTERTEK
- QUALITEST
- BLACK DUCK
- HCLSOFTWARE
- LEVELBLUE
- DXC TECHNOLOGY
- EINFOCHIPS
- CHECKMARX
- HACKERONE
- INVICTI
- DATAART
- COBALT
- PENTERA
- QUALIZEAL
- NOWSECURE
- FLUID ATTACKS
- ASTRA SECURITY
- 其他主要企业
- CONTRAST SECURITY
- VERACODE
- QUALYS
- OFFSEC
- NCC GROUP
- GITHUB
- BUGCROWD
- APPLAUSE
- RAPID7
- PARASOFT
- BREACHLOCK
- IMMUNIWEB
- PENTEST PEOPLE
- SAFEAEON
- REDTEAM.PL
第十九章:调查方法
第20章附录
The security testing market is projected to grow from USD 10.96 billion in 2025 to USD 40.99 billion by 2031 at a Compound Annual Growth Rate (CAGR) of 24.6% during the forecast period.
| Scope of the Report | |
|---|---|
| Years Considered for the Study | 2019-2031 |
| Base Year | 2024 |
| Forecast Period | 2025-2031 |
| Units Considered | Value (USD Billion) |
| Segments | Security Testing Type, Network Security Testing Type, Application Security Testing Type, Application Security Testing Tool, Deployment Mode, Organization Size, Vertical, and Region |
| Regions covered | North America, Europe, Asia Pacific, Middle East & Africa, Latin America |
The market is driven by the rapid adoption of web and mobile applications, which has significantly increased the number of exposed digital interfaces and heightened vulnerability to cyberattacks. In addition to this, organizations are under pressure to deliver frequent updates and new features without disrupting user experience. Accelerated release cycles increase the risk of introducing security flaws, making regular and structured security testing essential to maintain application reliability, performance, and user trust while supporting business agility.
"By application security testing type, the mobile application security testing segment is expected to witness the highest CAGR during the forecast period."
Mobile application security testing is growing at the fastest rate as enterprises increasingly rely on mobile apps to deliver customer services, payments, and workforce enablement. Mobile applications often process sensitive personal and financial data while operating across diverse devices and operating systems, which increases exposure to security weaknesses. According to Veracode, in January 2025, mobile applications assessed by enterprises frequently exhibited authentication and data handling flaws, reflecting persistent security gaps introduced during rapid development cycles. Mobile applications are also updated frequently to support new features, which raises the likelihood of introducing vulnerabilities that may impact performance and user trust.
The widespread adoption of bring your own device (BYOD) policies and remote work models has expanded mobile threat exposure across enterprise environments. Security testing is required to validate secure coding practices, API interactions, and backend integrations that support mobile applications. Mobile application security testing helps organizations identify vulnerabilities before deployment, protect user data, and maintain application reliability. As mobile platforms continue to serve as primary digital channels across BFSI, retail, healthcare, and government sectors, demand for specialized mobile security testing continues to accelerate.
"By network security type, the network penetration testing segment is projected to hold the largest market share in 2025."
Network penetration testing holds the largest market share due to its ability to simulate real-world attack scenarios and validate the effectiveness of security controls. Enterprises operate complex network environments that span on-premises infrastructure, cloud platforms, and remote access systems. According to Rapid7, in February 2025, organizations increasingly relied on penetration testing to identify weaknesses that automated scans often fail to uncover, such as misconfigurations and lateral movement paths. These insights are critical for understanding how attackers could exploit network weaknesses.
Network penetration testing supports compliance requirements across regulated industries, where organizations must demonstrate that defenses are tested against realistic threats. It also plays a key role in assessing the security impact of cloud migration and hybrid work environments. Penetration testing provides actionable findings that help security teams prioritize remediation efforts and improve incident preparedness. As cyberattacks become more targeted and sophisticated, enterprises continue to view network penetration testing as an essential component of proactive risk management and network resilience strategies.
By application security testing tool, the static application security testing (SAST) segment is expected to lead the market during the forecast period.
Static application security testing remains a core tool within application security programs as organizations seek to identify vulnerabilities early in the software development lifecycle. SAST analyzes source code to detect security weaknesses before applications are deployed, reducing remediation costs and development delays. According to Checkmarx, in April 2025, development teams increasingly embedded SAST into continuous integration pipelines to support faster releases while maintaining security standards. Early detection of flaws helps prevent vulnerabilities from reaching production environments.
SAST is widely adopted because it integrates directly into developer workflows and supports secure coding practices across large application portfolios. It is particularly valuable for identifying common coding errors, insecure functions, and compliance-related issues. As enterprises adopt agile and DevSecOps models, SAST enables consistent security testing without slowing development velocity. Its ability to scale across complex and distributed development environments reinforces its continued growth among application security testing tools.
Breakdown of Primaries
The study draws insights from a range of industry experts, including component suppliers, Tier 1 companies, and OEMs. The break-up of the primaries is as follows:
- By Company Type: Tier 1 - 20%, Tier 2 - 32%, and Tier 3 - 48%
- By Designation: C-level - 40%, Managerial Level, and Others - 60%
- By Region: North America - 40%, Europe - 25%, Asia Pacific - 20%, Middle East & Africa - 10%, Latin America - 5%
Major vendors in the security testing market include IBM (US), HCLTech (India), Black Duck (Synopsys) (US), OpenText (Canada), Cigniti Technologies (Coforge) (India), Qualitest (UK), Intertek (UK), DXC Technology (US), elnfochips (US), Checkmarx (US), HackerOne (US), Invicti (US), DataArt (US), Cobalt (US), LevelBlue (Trustwave) (US), Contrast Security (US), Veracode (US), Qualys (US), OffSec (US), NCC Group (UK), GitHub (US), Bugcrowd (US), Applause (US), Rapid7 (US), Parasoft (US), Breachlock (US), ImmuniWeb (Switzerland), Pentest People (UK), SafeAeon (US), REDTEAM.PL (Poland), Pentera (US), Qualizeal (US), Astra Security (US), NowSecure (US), and Fluid Attacks (US).
The study includes an in-depth competitive analysis of the key players in the security testing market, their company profiles, recent developments, and key market strategies.
Research Coverage
The report segments the security testing market and forecasts its size based on security testing type (network security testing, application security testing, device security testing, and social engineering security testing), network security testing type (network penetration testing, vulnerability scanning, Wi-Fi/wireless security testing, firewall security testing, network configuration auditing), application security testing type (mobile application security testing, web application security testing, api security testing, secure code review), application security testing tools (Runtime Application Self-Protection (RASP), Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Interactive Application Security Testing (IAST)), deployment mode (on-premises and cloud), organization size (large enterprises and SMEs), and vertical (BFSI, healthcare, government, IT & ITeS, telecommunications, manufacturing, retail & e-commerce, education, energy & utilities, and others).
The study also includes an in-depth competitive analysis of the market's key players, their company profiles, key observations related to product and business offerings, recent developments, and key market strategies.
Key Benefits of Buying the Report
The report will help market leaders/new entrants with information on the closest approximations of revenue numbers for the overall security testing market and its subsegments. This report will help stakeholders understand the competitive landscape and gain valuable insights to better position their businesses and plan suitable go-to-market strategies. The report also helps stakeholders understand the market pulse and provides information on key market drivers, restraints, challenges, and opportunities.
The report provides insights into the following pointers:
- Analysis of key drivers (Increased sophistication and variety in cyberattacks fueling demand for security testing, Rapid adoption of web and mobile applications vulnerable to cyberattack, Stringent government regulations to develop cybersecurity standards for data protection, Need to ensure seamless user experience with accelerated release cycles, Increasing reliance on third-party and open-source components), restraints (High false-positive rates from automated testing tools), opportunities (Emergence of technologies, such as AI and ML, in security testing, Increased adoption of cloud-based security testing, Integration of DevSecOps in software security testing, Growth of Security Testing as a Service (STaaS)), and challenges (Lack of skilled cybersecurity professionals, Fragmentation of security testing tools and platforms, Higher costs involved in executing security tests)
- Product Development/Innovation: Detailed insights on upcoming technologies, research & development activities, and product & service launches in the security testing market
- Market Development: Comprehensive information about lucrative markets - the report analyzes the security testing market across varied regions
- Market Diversification: Exhaustive information about new products & services, untapped geographies, recent developments, and investments in the security testing market
- Competitive Assessment: In-depth assessment of market shares, growth strategies, and service offerings of leading players in the security testing market, including IBM (US), Intertek (UK), Cigniti Technologies (Coforge) (US), OpenText (Canada), and Qualitest (UK)
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 STUDY OBJECTIVES
- 1.2 MARKET DEFINITION
- 1.3 STUDY SCOPE AND SEGMENTATION
- 1.3.1 MARKET SEGMENTATION
- 1.3.2 INCLUSIONS AND EXCLUSIONS
- 1.3.3 YEARS CONSIDERED
- 1.4 CURRENCY CONSIDERED
- 1.5 STAKEHOLDERS
- 1.6 SUMMARY OF CHANGES
2 EXECUTIVE SUMMARY
- 2.1 MARKET HIGHLIGHTS AND KEY INSIGHTS
- 2.2 KEY MARKET PARTICIPANTS: MAPPING OF STRATEGIC DEVELOPMENTS
- 2.3 DISRUPTIVE TRENDS SHAPING MARKET
- 2.4 HIGH-GROWTH SEGMENTS & EMERGING FRONTIERS
- 2.5 SNAPSHOT: GLOBAL MARKET SIZE, GROWTH RATE, AND FORECAST
3 PREMIUM INSIGHTS
- 3.1 ATTRACTIVE OPPORTUNITIES FOR PLAYERS IN SECURITY TESTING MARKET
- 3.2 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE
- 3.3 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE
- 3.4 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE
- 3.5 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOLS
- 3.6 SECURITY TESTING MARKET, BY VERTICAL
- 3.7 SECURITY TESTING MARKET, BY REGION
4 MARKET OVERVIEW
- 4.1 INTRODUCTION
- 4.2 MARKET DYNAMICS
- 4.2.1 DRIVERS
- 4.2.1.1 Increased sophistication and variety in cyberattacks fueling demand for security testing
- 4.2.1.2 Rapid adoption of web and mobile applications vulnerable to cyberattack
- 4.2.1.3 Stringent government regulations to develop cybersecurity standards for data protection
- 4.2.1.4 Need to ensure seamless user experience with accelerated release cycles
- 4.2.1.5 Increasing reliance on third-party and open-source components
- 4.2.2 RESTRAINTS
- 4.2.2.1 High false-positive rates from automated testing tools
- 4.2.3 OPPORTUNITIES
- 4.2.3.1 Emergence of technologies, such as AI and ML, in security testing
- 4.2.3.2 Increased adoption of cloud-based security testing
- 4.2.3.3 Integration of DevSecOps in software security testing
- 4.2.3.4 Growth of Security Testing-as-a-Service (STaaS)
- 4.2.4 CHALLENGES
- 4.2.4.1 Lack of skilled cybersecurity professionals
- 4.2.4.2 Fragmentation of security testing tools and platforms
- 4.2.4.3 Higher costs involved in executing security tests
- 4.2.1 DRIVERS
- 4.3 UNMET NEEDS AND WHITE SPACES
- 4.4 INTERCONNECTED MARKETS AND CROSS-SECTOR OPPORTUNITIES
- 4.4.1 INTERCONNECTED MARKETS
- 4.4.2 CROSS-SECTOR OPPORTUNITIES
- 4.5 STRATEGIC MOVES BY TIER -1/2/3 PLAYERS
- 4.5.1 CROSS-TIER STRATEGIC PATTERNS
- 4.5.2 STRATEGIC TRENDS
- 4.5.2.1 Adoption of DevSecOps and shift-left security
- 4.5.2.2 AI- and ML-driven security testing
- 4.5.2.3 Growth of cloud-native and continuous security testing
5 INDUSTRY TRENDS
- 5.1 PORTER'S FIVE FORCES ANALYSIS
- 5.1.1 THREAT OF NEW ENTRANTS
- 5.1.2 THREAT OF SUBSTITUTES
- 5.1.3 BARGAINING POWER OF SUPPLIERS
- 5.1.4 BARGAINING POWER OF BUYERS
- 5.1.5 INTENSITY OF COMPETITIVE RIVALRY
- 5.2 MACROECONOMIC INDICATORS
- 5.2.1 INTRODUCTION
- 5.2.2 GDP TRENDS AND FORECAST
- 5.2.3 TRENDS IN GLOBAL ICT INDUSTRY
- 5.2.4 TRENDS IN GLOBAL CYBERSECURITY INDUSTRY
- 5.3 VALUE CHAIN ANALYSIS
- 5.3.1 SECURITY TESTING TOOLS AND SERVICE PROVIDERS
- 5.3.2 TECHNOLOGY PROVIDERS
- 5.3.3 CONSULTANTS & INTEGRATORS
- 5.3.4 REGULATORY BODIES & STANDARDS
- 5.3.5 VARS/DISTRIBUTORS/RESELLERS
- 5.3.6 END USERS
- 5.4 ECOSYSTEM
- 5.5 PRICING ANALYSIS
- 5.5.1 AVERAGE SELLING PRICE TREND OF KEY PLAYERS, BY TESTING TYPE
- 5.5.2 INDICATIVE PRICING ANALYSIS, BY VENDOR
- 5.6 KEY CONFERENCES AND EVENTS IN 2026
- 5.7 TRENDS AND DISRUPTIONS IMPACTING CUSTOMER BUSINESS
- 5.8 INVESTMENT AND FUNDING SCENARIO
- 5.9 CASE STUDY ANALYSIS
- 5.9.1 SIEMENS HEALTHINEERS ENHANCED SECURITY OF APPLICATION DEVELOPMENT WITH CHECKMARX'S STATIC CODE ANALYSIS
- 5.9.2 THALES ALENIA SPACE BOOSTED CODE QUALITY AND SECURITY USING SYNOPSYS COVERITY AND BLACK DUCK
- 5.9.3 NORTHBRIDGE FINANCIAL IMPROVED API TESTING EFFICIENCY AND COVERAGE USING PARASOFT TOOLS
- 5.9.4 COHESION ENHANCED MOBILE APP SECURITY WITH NOWSECURE PLATFORM FOR SMART BUILDING SOLUTIONS
- 5.9.5 BUGCROWD HELPED RAPYD ELEVATE SECURITY WITH PENETRATION TESTING-AS-A-SERVICE AND BUG BOUNTY PROGRAMS
- 5.10 IMPACT OF 2025 US TARIFF - SECURITY TESTING MARKET
- 5.10.1 INTRODUCTION
- 5.10.2 KEY TARIFF RATES
- 5.10.3 PRICE IMPACT ANALYSIS
- 5.10.4 IMPACT ON COUNTRY/REGION
- 5.10.4.1 North America
- 5.10.4.2 Europe
- 5.10.4.3 Asia Pacific
- 5.10.5 IMPACT ON END-USE INDUSTRIES
6 TECHNOLOGICAL ADVANCEMENTS, AI-DRIVEN IMPACT, PATENTS, INNOVATIONS, AND FUTURE APPLICATIONS
- 6.1 TECHNOLOGY ANALYSIS
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.1.1.1 Static Application Security Testing (SAST)
- 6.1.1.2 Dynamic Application Security Testing (DAST)
- 6.1.2 COMPLEMENTARY TECHNOLOGIES
- 6.1.2.1 Threat intelligence
- 6.1.2.2 DevSecOps
- 6.1.3 ADJACENT TECHNOLOGIES
- 6.1.3.1 Artificial Intelligence (AI) and Machine Learning (ML)
- 6.1.3.2 Blockchain
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.2 TECHNOLOGY ROADMAP
- 6.2.1 SHORT-TERM (2026-2027) | FOUNDATION & EARLY COMMERCIALIZATION
- 6.2.2 MID-TERM (2027-2030) SCALING, INTELLIGENCE & ECOSYSTEM EXPANSION
- 6.2.3 LONG-TERM (2030-2035+) | AUTONOMOUS, REAL-TIME & ADAPTIVE SECURITY
- 6.3 PATENT ANALYSIS
- 6.4 FUTURE APPLICATIONS
- 6.4.1 AUTONOMOUS & AI-DRIVEN SECURITY TESTING PLATFORMS
- 6.4.2 DATA-DRIVEN SECURITY ANALYTICS & PREDICTIVE RISK INSIGHTS
- 6.4.3 ADVANCED THREAT SIMULATION & ATTACK EMULATION
- 6.4.4 AI-DRIVEN ADAPTIVE SECURITY TESTING & RISK PRIORITIZATION
- 6.4.5 CONTINUOUS SECURITY VALIDATION & DEVSECOPS-INTEGRATED TESTING
- 6.5 IMPACT OF AI/GEN AI ON SECURITY TESTING MARKET
- 6.5.1 BEST PRACTICES IN SECURITY TESTING MARKET
- 6.5.2 CASE STUDIES OF AI IMPLEMENTATION IN SECURITY TESTING MARKET
- 6.5.3 INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
- 6.5.4 CLIENTS' READINESS TO ADOPT GENERATIVE AI IN SECURITY TESTING MARKET
- 6.6 SUCCESS STORIES AND REAL-WORLD APPLICATIONS
- 6.6.1 CHECKMARX: SECURE SOFTWARE DEVELOPMENT TRANSFORMATION FOR GLOBAL ENTERPRISE
- 6.6.2 RAPID7: CLOUD-NATIVE VULNERABILITY MANAGEMENT FOR GLOBAL ENTERPRISE
7 REGULATORY LANDSCAPE
- 7.1 REGIONAL REGULATIONS AND COMPLIANCE
- 7.1.1 REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- 7.1.2 INDUSTRY STANDARDS
8 CONSUMER LANDSCAPE & BUYER BEHAVIOR
- 8.1 DECISION-MAKING PROCESS
- 8.2 BUYER STAKEHOLDERS AND BUYING EVALUATION CRITERIA
- 8.2.1 KEY STAKEHOLDERS IN BUYING PROCESS
- 8.2.2 BUYING CRITERIA
- 8.3 ADOPTION BARRIERS & INTERNAL CHALLENGES
- 8.4 UNMET NEEDS IN VARIOUS END-USE INDUSTRIES
- 8.5 MARKET PROFITABILITY
- 8.5.1 REVENUE POTENTIAL
- 8.5.2 COST DYNAMICS
- 8.5.3 MARGIN OPPORTUNITIES IN KEY APPLICATIONS
9 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE
- 9.1 INTRODUCTION
- 9.1.1 SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 9.2 NETWORK SECURITY TESTING
- 9.2.1 RAPID GROWTH OF CYBERATTACKS AND NEED TO ADDRESS NETWORK SECURITY ISSUES AND MINIMIZE DATA LOSS TO PROPEL MARKET
- 9.3 APPLICATION SECURITY TESTING
- 9.3.1 NEED TO IDENTIFY VULNERABILITIES, THREATS, AND RISKS IN INTERNAL AND EXTERNAL APPLICATIONS TO FUEL MARKET GROWTH
- 9.4 DEVICE SECURITY TESTING
- 9.4.1 ADVANCEMENTS IN DEVICE SECURITY TESTING WITH POST-QUANTUM CRYPTOGRAPHY SOLUTIONS TO BOOST MARKET GROWTH
- 9.5 SOCIAL ENGINEERING TESTING
- 9.5.1 SOCIAL ENGINEERING TESTING TO MITIGATE RISKS WITH ENHANCED PENETRATION TESTING
10 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE
- 10.1 INTRODUCTION
- 10.1.1 NETWORK SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 10.2 NETWORK PENETRATION TESTING
- 10.2.1 NETWORK PENETRATION TESTING TO HELP ETHICAL HACKERS SIMULATE CYBERATTACKS TO UNCOVER VULNERABILITIES
- 10.3 VULNERABILITY SCANNING
- 10.3.1 NETWORK VULNERABILITY SCANNING SOLUTIONS TO IDENTIFY AND MITIGATE POTENTIAL THREATS
- 10.4 WI-FI/WIRELESS SECURITY TESTING
- 10.4.1 NEED TO IDENTIFY VULNERABILITIES IN WIRELESS NETWORKS AND ENSURE PROTECTION OF SENSITIVE DATA AND SYSTEMS TO BOLSTER MARKET GROWTH
- 10.5 FIREWALL SECURITY TESTING
- 10.5.1 FIREWALL SECURITY TESTING TO EVALUATE EFFECTIVENESS OF FIREWALLS IN PROTECTING NETWORKS FROM UNAUTHORIZED ACCESS AND CYBER THREATS
- 10.6 NETWORK CONFIGURATION AUDITING
- 10.6.1 NETWORK CONFIGURATION AUDITING TO SCAN NETWORK INFRASTRUCTURE, CHECK FOR COMPLIANCE WITH SECURITY POLICIES, AND IDENTIFY DEVICES WITH OUTDATED FIRMWARE OR INSECURE CONFIGURATIONS
11 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE
- 11.1 INTRODUCTION
- 11.1.1 APPLICATION SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 11.2 MOBILE APPLICATION SECURITY TESTING
- 11.2.1 MOBILE APPLICATION SECURITY TESTING TO PROTECT SENSITIVE DATA, HELP ORGANIZATIONS ADHERE TO REGULATIONS, AND ENHANCE SECURITY POSTURE
- 11.3 WEB APPLICATION SECURITY TESTING
- 11.3.1 WEB APPLICATION SECURITY TESTING TO HELP PREVENT DATA BREACHES, ENSURE COMPLIANCE WITH INDUSTRY STANDARDS, AND MAINTAIN USER TRUST
- 11.4 API SECURITY TESTING
- 11.4.1 API SECURITY TESTING TO VALIDATE API ENDPOINTS TO DETECT VULNERABILITIES THAT ATTACKERS MIGHT EXPLOIT AND ENSURE SAFE INTEGRATION WITH DEVELOPMENT PROCESSES
- 11.5 SECURE CODE REVIEW
- 11.5.1 SECURE CODE REVIEW TO HELP DEVELOPERS ADDRESS ISSUES EARLY BY ANALYZING CODE FOR POTENTIAL SECURITY FLAWS AND PREVENTING FUTURE BREACHES AND ATTACKS
12 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL
- 12.1 INTRODUCTION
- 12.1.1 APPLICATION SECURITY TESTING TOOL: SECURITY TESTING MARKET DRIVERS
- 12.2 RUNTIME APPLICATION SELF-PROTECTION (RASP)
- 12.2.1 RASP TO PROTECT APPLICATIONS IN REAL-TIME BY DETECTING AND BLOCKING ATTACKS
- 12.3 STATIC APPLICATION SECURITY TESTING (SAST)
- 12.3.1 NEXT-GEN SAST TOOLS TO ENHANCE SPEED AND ACCURACY AND HELP IDENTIFY AND FIX SECURITY FLAWS EARLY
- 12.4 DYNAMIC APPLICATION SECURITY TESTING (DAST)
- 12.4.1 DAST TOOLS TO EVALUATE WEB APPLICATIONS WHILE RUNNING AND SIMULATE REAL-WORLD ATTACKS TO IDENTIFY VULNERABILITIES
- 12.5 INTERACTIVE APPLICATION SECURITY TESTING (IAST)
- 12.5.1 INTERACTIVE APPLICATION SECURITY TESTING (IAST) TO COMBINE STATIC AND DYNAMIC TESTING ELEMENTS TO UNCOVER WEB APPLICATION VULNERABILITIES DURING RUNTIME INTEGRATION
13 SECURITY TESTING MARKET, BY DEPLOYMENT MODE
- 13.1 INTRODUCTION
- 13.1.1 DEPLOYMENT MODE: SECURITY TESTING MARKET DRIVERS
- 13.2 ON-PREMISES
- 13.2.1 ON-PREMISE DEPLOYMENT IS PARTICULARLY IMPORTANT FOR LEGACY SYSTEMS AND OPERATIONAL TECHNOLOGY ENVIRONMENTS WHERE EXTERNAL CONNECTIVITY IS LIMITED
- 13.3 CLOUD
- 13.3.1 CONTINUOUS VISIBILITY AND VULNERABILITY MANAGEMENT ACROSS DISTRIBUTED ENVIRONMENTS TO DRIVE MARKET GROWTH
14 SECURITY TESTING MARKET, BY ORGANIZATION SIZE
- 14.1 INTRODUCTION
- 14.1.1 ORGANIZATION SIZE: SECURITY TESTING MARKET DRIVERS
- 14.2 LARGE ENTERPRISES
- 14.2.1 TREND OF DIGITALIZATION AND SECURITY TESTING, GROWING CONNECTIVITY OF BANDWIDTHS, AND MOBILITY TRENDS IN LARGE ENTERPRISES TO DRIVE MARKET
- 14.3 SMALL AND MEDIUM-SIZED ENTERPRISES
- 14.3.1 COMPLEX IT ENVIRONMENTS AND NEED TO COMPLY WITH STRINGENT DATA PROTECTION REGULATIONS TO PROPEL MARKET
15 SECURITY TESTING MARKET, BY VERTICAL
- 15.1 INTRODUCTION
- 15.1.1 VERTICAL: SECURITY TESTING MARKET DRIVERS
- 15.2 BANKING, FINANCIAL SERVICES, AND INSURANCE
- 15.2.1 RELIANCE ON DIGITAL PLATFORMS FOR SMART BANKING, INTERNET BANKING, AND MOBILE TRANSACTIONS INCREASING CYBERATTACKS TO FOSTER MARKET GROWTH
- 15.3 HEALTHCARE
- 15.3.1 CRITICAL NATURE OF OPERATIONS AND SENSITIVE NATURE OF PATIENT DATA TO DRIVE DEMAND FOR SECURITY TESTING
- 15.4 GOVERNMENT & DEFENSE
- 15.4.1 ESCALATING CYBER THREATS AND EVOLVING REGULATORY REQUIREMENTS TO BOOST DEMAND FOR SECURITY TESTING SOLUTIONS
- 15.5 IT & ITES
- 15.5.1 CONTINUOUS DEVELOPMENT OF NEW SOLUTIONS AND EXTENSIVE USE OF WEB AND MOBILE APPLICATIONS TO RISE DEMAND FOR SECURITY TESTING SOLUTIONS
- 15.6 TELECOMMUNICATIONS
- 15.6.1 NEED TO PROTECT AGAINST EVOLVING THREATS, COMPLY WITH REGULATORY STANDARDS, AND ENSURE RELIABILITY OF SERVICES TO BOOST MARKET GROWTH
- 15.7 MANUFACTURING
- 15.7.1 SECURITY TESTING TO HELP ADHERE TO COMPLIANCE REQUIREMENTS, PROTECT AGAINST POTENTIAL DATA BREACHES, AND ENSURE OVERALL SECURITY OF MANUFACTURING OPERATIONS
- 15.8 RETAIL & ECOMMERCE
- 15.8.1 DIGITAL TRANSFORMATION IN RETAIL AND HIGH-VALUE TRANSACTIONS TO ACCELERATE MARKET GROWTH
- 15.9 EDUCATION
- 15.9.1 SURGE IN VULNERABILITIES IN ELEARNING SECTOR AND SHIFT TOWARD DIGITAL TECHNOLOGIES FOR EDUCATIONAL DATA TO PROPEL MARKET
- 15.10 ENERGY & UTILITIES
- 15.10.1 RAPID INCORPORATION OF DIGITAL TECHNOLOGIES INCREASING EXPOSURE TO CYBERATTACKS TO DRIVE MARKET
- 15.11 OTHER VERTICALS
16 SECURITY TESTING MARKET, BY REGION
- 16.1 INTRODUCTION
- 16.2 NORTH AMERICA
- 16.2.1 NORTH AMERICA: SECURITY TESTING MARKET DRIVERS
- 16.2.2 US
- 16.2.2.1 Focus on strategic developments and rising incidents of cyber threats to drive market
- 16.2.3 CANADA
- 16.2.3.1 Emphasis on regulatory frameworks and critical infrastructure security to drive market
- 16.3 EUROPE
- 16.3.1 EUROPE: SECURITY TESTING MARKET DRIVERS
- 16.3.2 UK
- 16.3.2.1 Strategic advancement in security testing through AI collaboration to boost market growth
- 16.3.3 GERMANY
- 16.3.3.1 Rapid digital transformation and surge in cyber threats to boost demand for security testing
- 16.3.4 FRANCE
- 16.3.4.1 Expanding cybersecurity landscape to boost demand for security testing solutions
- 16.3.5 ITALY
- 16.3.5.1 Rise in sophisticated cyberattacks and demand for cybersecurity in automotive & industrial sectors to propel market
- 16.3.6 REST OF EUROPE
- 16.4 ASIA PACIFIC
- 16.4.1 ASIA PACIFIC: SECURITY TESTING MARKET DRIVERS
- 16.4.2 CHINA
- 16.4.2.1 Rapid digital expansion and increasing cyber risks to drive security testing demand
- 16.4.3 JAPAN
- 16.4.3.1 Increasing cyber incidents and digital infrastructure expansion to drive security testing demand
- 16.4.4 INDIA
- 16.4.4.1 Advancements in India's security testing frameworks and implementation of new regulations to propel market
- 16.4.5 REST OF ASIA PACIFIC
- 16.5 MIDDLE EAST & AFRICA
- 16.5.1 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET DRIVERS
- 16.5.2 GCC
- 16.5.2.1 Implementation of 'Vision for Regional Security' to accelerate market growth
- 16.5.2.2 KSA
- 16.5.2.2.1 Growing digital transformation and rising instances of cyber threats to drive market
- 16.5.2.3 UAE
- 16.5.2.3.1 Increasing smart infrastructure expansion to drive security testing demand
- 16.5.2.4 Rest of GCC countries
- 16.5.3 SOUTH AFRICA
- 16.5.3.1 Growing prevalence of phishing attacks, social engineering scams, and phishing scams to propel market
- 16.5.4 REST OF MIDDLE EAST & AFRICA
- 16.6 LATIN AMERICA
- 16.6.1 LATIN AMERICA: SECURITY TESTING MARKET DRIVERS
- 16.6.2 BRAZIL
- 16.6.2.1 Rise in digital adoption to foster market growth
- 16.6.3 MEXICO
- 16.6.3.1 State-driven cyber-espionage and hacktivism and vulnerability of government organizations to drive market growth
- 16.6.4 REST OF LATIN AMERICA
17 COMPETITIVE LANDSCAPE
- 17.1 KEY PLAYER STRATEGIES/RIGHT TO WIN, 2024-2026
- 17.2 REVENUE ANALYSIS, 2020-2024
- 17.3 MARKET SHARE ANALYSIS, 2025
- 17.4 BRAND COMPARISON
- 17.5 COMPANY EVALUATION MATRIX: KEY PLAYERS, 2025
- 17.5.1 STARS
- 17.5.2 EMERGING LEADERS
- 17.5.3 PERVASIVE PLAYERS
- 17.5.4 PARTICIPANTS
- 17.5.5 COMPANY FOOTPRINT: KEY PLAYERS, 2025
- 17.5.5.1 Company footprint
- 17.5.5.2 Security testing type footprint
- 17.5.5.3 Deployment mode footprint
- 17.5.5.4 Vertical footprint
- 17.5.5.5 Regional footprint
- 17.6 COMPANY EVALUATION MATRIX: STARTUPS/SMES, 2025
- 17.6.1 PROGRESSIVE COMPANIES
- 17.6.2 RESPONSIVE COMPANIES
- 17.6.3 DYNAMIC COMPANIES
- 17.6.4 STARTING BLOCKS
- 17.6.5 COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2025
- 17.6.5.1 Key startups/SMEs
- 17.6.5.2 Competitive benchmarking of key startups/SMEs
- 17.7 COMPANY VALUATION AND FINANCIAL METRICS
- 17.7.1 COMPANY VALUATION
- 17.7.2 FINANCIAL METRICS USING EV/EBIDTA
- 17.8 COMPETITIVE SCENARIO AND TRENDS
- 17.8.1 PRODUCT LAUNCHES AND ENHANCEMENTS
- 17.8.2 DEALS
18 COMPANY PROFILES
- 18.1 KEY PLAYERS
- 18.1.1 IBM
- 18.1.1.1 Business overview
- 18.1.1.2 Products/Solutions/Services offered
- 18.1.1.3 Recent developments
- 18.1.1.3.1 Deals
- 18.1.1.4 MnM view
- 18.1.1.4.1 Right to win
- 18.1.1.4.2 Strategic choices
- 18.1.1.4.3 Weaknesses and competitive threats
- 18.1.2 OPENTEXT
- 18.1.2.1 Business overview
- 18.1.2.2 Products/Solutions/Services offered
- 18.1.2.3 Recent developments
- 18.1.2.3.1 Product launches
- 18.1.2.4 MnM view
- 18.1.2.4.1 Right to win
- 18.1.2.4.2 Strategic choices
- 18.1.2.4.3 Weaknesses and competitive threats
- 18.1.3 CIGNITI TECHNOLOGIES
- 18.1.3.1 Business overview
- 18.1.3.2 Products/Solutions/Services offered
- 18.1.3.3 MnM view
- 18.1.3.3.1 Right to win
- 18.1.3.3.2 Strategic choices
- 18.1.3.3.3 Weaknesses and competitive threats
- 18.1.4 INTERTEK
- 18.1.4.1 Business overview
- 18.1.4.2 Products/Solutions/Services offered
- 18.1.4.3 Recent developments
- 18.1.4.3.1 Product launches
- 18.1.4.4 MnM view
- 18.1.4.4.1 Right to win
- 18.1.4.4.2 Strategic choices
- 18.1.4.4.3 Weaknesses and competitive threats
- 18.1.5 QUALITEST
- 18.1.5.1 Business overview
- 18.1.5.2 Products/Solutions/Services offered
- 18.1.5.3 MnM view
- 18.1.5.3.1 Right to win
- 18.1.5.3.2 Strategic choices
- 18.1.5.3.3 Weaknesses and competitive threats
- 18.1.6 BLACK DUCK
- 18.1.6.1 Business overview
- 18.1.6.2 Products/Solutions/Services offered
- 18.1.7 HCLSOFTWARE
- 18.1.7.1 Business overview
- 18.1.7.2 Products/Solutions/Services offered
- 18.1.7.3 Recent developments
- 18.1.7.3.1 Deals
- 18.1.8 LEVELBLUE
- 18.1.8.1 Business overview
- 18.1.8.2 Products/Solutions/Services offered
- 18.1.8.3 Recent developments
- 18.1.8.3.1 Deals
- 18.1.9 DXC TECHNOLOGY
- 18.1.9.1 Business overview
- 18.1.9.2 Products/Solutions/Services offered
- 18.1.9.3 Recent developments
- 18.1.9.3.1 Deals
- 18.1.10 EINFOCHIPS
- 18.1.10.1 Business overview
- 18.1.10.2 Products/Solutions/Services offered
- 18.1.11 CHECKMARX
- 18.1.11.1 Business overview
- 18.1.11.2 Products/Solutions/Services offered
- 18.1.11.3 Recent developments
- 18.1.11.3.1 Product launches
- 18.1.11.3.2 Deals
- 18.1.12 HACKERONE
- 18.1.12.1 Business overview
- 18.1.12.2 Products/Solutions/Services offered
- 18.1.12.3 Recent developments
- 18.1.12.3.1 Product launches
- 18.1.12.3.2 Deals
- 18.1.13 INVICTI
- 18.1.13.1 Business overview
- 18.1.13.2 Products/Solutions/Services offered
- 18.1.13.3 Recent developments
- 18.1.13.3.1 Product launches
- 18.1.13.3.2 Deals
- 18.1.14 DATAART
- 18.1.14.1 Business overview
- 18.1.14.2 Products/Solutions/Services offered
- 18.1.15 COBALT
- 18.1.15.1 Business overview
- 18.1.15.2 Products/Solutions/Services offered
- 18.1.15.3 Recent developments
- 18.1.15.3.1 Product launches
- 18.1.15.3.2 Deals
- 18.1.16 PENTERA
- 18.1.17 QUALIZEAL
- 18.1.18 NOWSECURE
- 18.1.19 FLUID ATTACKS
- 18.1.20 ASTRA SECURITY
- 18.1.1 IBM
- 18.2 OTHER KEY PLAYERS
- 18.2.1 CONTRAST SECURITY
- 18.2.2 VERACODE
- 18.2.3 QUALYS
- 18.2.4 OFFSEC
- 18.2.5 NCC GROUP
- 18.2.6 GITHUB
- 18.2.7 BUGCROWD
- 18.2.8 APPLAUSE
- 18.2.9 RAPID7
- 18.2.10 PARASOFT
- 18.2.11 BREACHLOCK
- 18.2.12 IMMUNIWEB
- 18.2.13 PENTEST PEOPLE
- 18.2.14 SAFEAEON
- 18.2.15 REDTEAM.PL
19 RESEARCH METHODOLOGY
- 19.1 RESEARCH DATA
- 19.1.1 SECONDARY DATA
- 19.1.2 PRIMARY DATA
- 19.1.2.1 Breakdown of primary profiles
- 19.1.2.2 Key industry insights
- 19.2 DATA TRIANGULATION
- 19.3 MARKET SIZE ESTIMATION
- 19.3.1 TOP-DOWN APPROACH
- 19.3.2 BOTTOM-UP APPROACH
- 19.4 MARKET FORECAST
- 19.5 RESEARCH ASSUMPTIONS
- 19.6 RESEARCH LIMITATIONS
20 APPENDIX
- 20.1 DISCUSSION GUIDE
- 20.2 KNOWLEDGESTORE: MARKETSANDMARKETS' SUBSCRIPTION PORTAL
- 20.3 CUSTOMIZATION OPTIONS
- 20.4 RELATED REPORTS
- 20.5 AUTHOR DETAILS
List of Tables
- TABLE 1 INCLUSIONS AND EXCLUSIONS
- TABLE 2 USD EXCHANGE RATES, 2021-2025
- TABLE 3 UNMET NEEDS AND WHITE SPACES IN LEARNING MANAGEMENT SYSTEM MARKET
- TABLE 4 STRATEGIC MOVES BY PLAYERS IN LEARNING MANAGEMENT SYSTEM MARKET
- TABLE 5 CROSS-TIER STRATEGIC PATTERNS OF VENDORS
- TABLE 6 PORTER'S FIVE FORCES' IMPACT ON SECURITY TESTING MARKET
- TABLE 7 GDP PERCENTAGE CHANGE, BY KEY COUNTRY, 2021-2030
- TABLE 8 SECURITY TESTING MARKET: ECOSYSTEM
- TABLE 9 AVERAGE SELLING PRICES OF KEY PLAYERS FOR TOP TWO TESTING TYPES (USD)
- TABLE 10 INDICATIVE PRICING LEVELS OF SECURITY TESTING SOLUTIONS
- TABLE 11 PRICING MODELS OF BUGCROWD
- TABLE 12 PRICING MODELS OF BREACHLOCK
- TABLE 13 SECURITY TESTING MARKET: DETAILED LIST OF CONFERENCES AND EVENTS, 2026
- TABLE 14 KEY TARIFF RATES
- TABLE 15 LIST OF TOP PATENTS IN SECURITY TESTING MARKET, 2023-2025
- TABLE 16 TOP USE CASES AND MARKET POTENTIAL
- TABLE 17 BEST PRACTICES: COMPANIES IMPLEMENTING USE CASES
- TABLE 18 SECURITY TESTING MARKET: CASE STUDIES RELATED TO GEN AI IMPLEMENTATION
- TABLE 19 INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
- TABLE 20 NORTH AMERICA: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- TABLE 21 EUROPE: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- TABLE 22 ASIA PACIFIC: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- TABLE 23 MIDDLE EAST & AFRICA: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- TABLE 24 LATIN AMERICA: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- TABLE 25 GLOBAL INDUSTRY STANDARDS IN SECURITY TESTING MARKET
- TABLE 26 INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE USER TYPES (%)
- TABLE 27 KEY BUYING CRITERIA FOR TOP THREE USER TYPES
- TABLE 28 UNMET NEEDS IN SECURITY TESTING MARKET, BY END-USE INDUSTRY
- TABLE 29 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 30 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 31 NETWORK SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 32 NETWORK SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 33 APPLICATION SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 34 APPLICATION SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 35 DEVICE SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 36 DEVICE SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 37 SOCIAL ENGINEERING TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 38 SOCIAL ENGINEERING TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 39 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 40 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 41 NETWORK PENETRATION TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 42 NETWORK PENETRATION TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 43 VULNERABILITY SCANNING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 44 VULNERABILITY SCANNING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 45 WI-FI/WIRELESS SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 46 WI-FI/WIRELESS SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 47 FIREWALL SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 48 FIREWALL SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 49 NETWORK CONFIGURATION AUDITING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 50 NETWORK CONFIGURATION AUDITING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 51 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 52 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 53 MOBILE APPLICATION SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 54 MOBILE APPLICATION SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 55 WEB APPLICATION SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 56 WEB APPLICATION SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 57 API SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 58 API SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 59 SECURE CODE REVIEW MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 60 SECURE CODE REVIEW MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 61 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 62 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 63 RUNTIME APPLICATION SELF-PROTECTION (RASP) MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 64 RUNTIME APPLICATION SELF-PROTECTION (RASP) MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 65 STATIC APPLICATION SECURITY TESTING (SAST) MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 66 STATIC APPLICATION SECURITY TESTING (SAST) MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 67 DYNAMIC APPLICATION SECURITY TESTING (DAST) MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 68 DYNAMIC APPLICATION SECURITY TESTING (DAST) MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 69 INTERACTIVE APPLICATION SECURITY TESTING (IAST) MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 70 INTERACTIVE APPLICATION SECURITY TESTING (IAST) MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 71 SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 72 SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 73 ON-PREMISE SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 74 ON-PREMISE SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 75 CLOUD-BASED SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 76 CLOUD-BASED SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 77 SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 78 SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 79 SECURITY TESTING MARKET FOR LARGE ENTERPRISES, BY REGION, 2019-2024 (USD MILLION)
- TABLE 80 SECURITY TESTING MARKET FOR LARGE ENTERPRISES, BY REGION, 2025-2031 (USD MILLION)
- TABLE 81 SECURITY TESTING MARKET FOR SMALL AND MEDIUM-SIZED ENTERPRISES, BY REGION, 2019-2024 (USD MILLION)
- TABLE 82 SECURITY TESTING MARKET FOR SMALL AND MEDIUM-SIZED ENTERPRISES, BY REGION, 2025-2031 (USD MILLION)
- TABLE 83 SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 84 SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 85 SECURITY TESTING MARKET IN BANKING, FINANCIAL SERVICES, AND INSURANCE, BY REGION, 2019-2024 (USD MILLION)
- TABLE 86 SECURITY TESTING MARKET IN BANKING, FINANCIAL SERVICES, AND INSURANCE, BY REGION, 2025-2031 (USD MILLION)
- TABLE 87 SECURITY TESTING MARKET IN HEALTHCARE, BY REGION, 2019-2024 (USD MILLION)
- TABLE 88 SECURITY TESTING MARKET IN HEALTHCARE, BY REGION, 2025-2031 (USD MILLION)
- TABLE 89 SECURITY TESTING MARKET IN GOVERNMENT & DEFENSE, BY REGION, 2019-2024 (USD MILLION)
- TABLE 90 SECURITY TESTING MARKET IN GOVERNMENT & DEFENSE, BY REGION, 2025-2031 (USD MILLION)
- TABLE 91 SECURITY TESTING MARKET IN IT & ITES, BY REGION, 2019-2024 (USD MILLION)
- TABLE 92 SECURITY TESTING MARKET IN IT & ITES, BY REGION, 2025-2031 (USD MILLION)
- TABLE 93 SECURITY TESTING MARKET IN TELECOMMUNICATIONS, BY REGION, 2019-2024 (USD MILLION)
- TABLE 94 SECURITY TESTING MARKET IN TELECOMMUNICATIONS, BY REGION, 2025-2031 (USD MILLION)
- TABLE 95 SECURITY TESTING MARKET IN MANUFACTURING, BY REGION, 2019-2024 (USD MILLION)
- TABLE 96 SECURITY TESTING MARKET IN MANUFACTURING, BY REGION, 2025-2031 (USD MILLION)
- TABLE 97 SECURITY TESTING MARKET IN RETAIL & ECOMMERCE, BY REGION, 2019-2024 (USD MILLION)
- TABLE 98 SECURITY TESTING MARKET IN RETAIL & ECOMMERCE, BY REGION, 2025-2031 (USD MILLION)
- TABLE 99 SECURITY TESTING MARKET IN EDUCATION, BY REGION, 2019-2024 (USD MILLION)
- TABLE 100 SECURITY TESTING MARKET IN EDUCATION, BY REGION, 2025-2031 (USD MILLION)
- TABLE 101 SECURITY TESTING MARKET IN ENERGY & UTILITIES, BY REGION, 2019-2024 (USD MILLION)
- TABLE 102 SECURITY TESTING MARKET IN ENERGY & UTILITIES, BY REGION, 2025-2031 (USD MILLION)
- TABLE 103 SECURITY TESTING MARKET IN OTHER VERTICALS, BY REGION, 2019-2024 (USD MILLION)
- TABLE 104 SECURITY TESTING MARKET IN OTHER VERTICALS, BY REGION, 2025-2031 (USD MILLION)
- TABLE 105 SECURITY TESTING MARKET, BY REGION, 2019-2024 (USD MILLION)
- TABLE 106 SECURITY TESTING MARKET, BY REGION, 2025-2031 (USD MILLION)
- TABLE 107 NORTH AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 108 NORTH AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 109 NORTH AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 110 NORTH AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 111 NORTH AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 112 NORTH AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 113 NORTH AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 114 NORTH AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 115 NORTH AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 116 NORTH AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 117 NORTH AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 118 NORTH AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 119 NORTH AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 120 NORTH AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 121 NORTH AMERICA: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 122 NORTH AMERICA: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 123 US: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 124 US: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 125 US: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 126 US: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 127 US: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 128 US: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 129 US: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 130 US: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 131 US: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 132 US: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 133 US: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 134 US: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 135 US: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 136 US: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 137 CANADA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 138 CANADA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 139 CANADA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 140 CANADA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 141 CANADA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 142 CANADA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 143 CANADA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 144 CANADA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 145 CANADA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 146 CANADA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 147 CANADA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 148 CANADA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 149 CANADA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 150 CANADA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 151 EUROPE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 152 EUROPE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 153 EUROPE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 154 EUROPE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 155 EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 156 EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 157 EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 158 EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 159 EUROPE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 160 EUROPE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 161 EUROPE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 162 EUROPE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 163 EUROPE: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 164 EUROPE: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 165 EUROPE: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 166 EUROPE: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 167 UK: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 168 UK: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 169 UK: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 170 UK: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 171 UK: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 172 UK: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 173 UK: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 174 UK: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 175 UK: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 176 UK: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 177 UK: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 178 UK: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 179 UK: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 180 UK: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 181 GERMANY: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 182 GERMANY: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 183 GERMANY: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 184 GERMANY: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 185 GERMANY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 186 GERMANY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 187 GERMANY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 188 GERMANY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 189 GERMANY: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 190 GERMANY: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 191 GERMANY: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 192 GERMANY: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 193 GERMANY: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 194 GERMANY: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 195 FRANCE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 196 FRANCE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 197 FRANCE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 198 FRANCE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 199 FRANCE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 200 FRANCE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 201 FRANCE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 202 FRANCE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 203 FRANCE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 204 FRANCE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 205 FRANCE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 206 FRANCE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 207 FRANCE: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 208 FRANCE: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 209 ITALY: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 210 ITALY: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 211 ITALY: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 212 ITALY: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 213 ITALY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 214 ITALY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 215 ITALY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 216 ITALY: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 217 ITALY: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 218 ITALY: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 219 ITALY: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 220 ITALY: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 221 ITALY: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 222 ITALY: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 223 REST OF EUROPE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 224 REST OF EUROPE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 225 REST OF EUROPE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 226 REST OF EUROPE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 227 REST OF EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 228 REST OF EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 229 REST OF EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 230 REST OF EUROPE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 231 REST OF EUROPE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 232 REST OF EUROPE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 233 REST OF EUROPE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 234 REST OF EUROPE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 235 REST OF EUROPE: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 236 REST OF EUROPE: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 237 ASIA PACIFIC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 238 ASIA PACIFIC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 239 ASIA PACIFIC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 240 ASIA PACIFIC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 241 ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 242 ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 243 ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 244 ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 245 ASIA PACIFIC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 246 ASIA PACIFIC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 247 ASIA PACIFIC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 248 ASIA PACIFIC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 249 ASIA PACIFIC: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 250 ASIA PACIFIC: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 251 ASIA PACIFIC: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 252 ASIA PACIFIC: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 253 CHINA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 254 CHINA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 255 CHINA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 256 CHINA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 257 CHINA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 258 CHINA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 259 CHINA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 260 CHINA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 261 CHINA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 262 CHINA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 263 CHINA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 264 CHINA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 265 CHINA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 266 CHINA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 267 JAPAN: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 268 JAPAN: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 269 JAPAN: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 270 JAPAN: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 271 JAPAN: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 272 JAPAN: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 273 JAPAN: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 274 JAPAN: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 275 JAPAN: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 276 JAPAN: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 277 JAPAN: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 278 JAPAN: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 279 JAPAN: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 280 JAPAN: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 281 INDIA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 282 INDIA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 283 INDIA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 284 INDIA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 285 INDIA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 286 INDIA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 287 INDIA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 288 INDIA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 289 INDIA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 290 INDIA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 291 INDIA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 292 INDIA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 293 INDIA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 294 INDIA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 295 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 296 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 297 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 298 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 299 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 300 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 301 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 302 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 303 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 304 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 305 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 306 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 307 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 308 REST OF ASIA PACIFIC: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 309 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 310 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 311 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 312 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 313 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 314 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 315 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 316 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 317 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 318 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 319 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 320 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 321 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 322 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 323 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 324 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 325 GCC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 326 GCC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 327 GCC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 328 GCC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 329 GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 330 GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 331 GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 332 GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 333 GCC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 334 GCC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 335 GCC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 336 GCC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 337 GCC: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 338 GCC: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 339 GCC: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 340 GCC: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 341 KSA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 342 KSA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 343 KSA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 344 KSA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 345 KSA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 346 KSA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 347 KSA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 348 KSA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 349 KSA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 350 KSA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 351 KSA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 352 KSA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 353 KSA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 354 KSA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 355 UAE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 356 UAE: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 357 UAE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 358 UAE: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 359 UAE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 360 UAE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 361 UAE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 362 UAE: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 363 UAE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 364 UAE: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 365 UAE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 366 UAE: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 367 UAE: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 368 UAE: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 369 REST OF GCC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 370 REST OF GCC: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 371 REST OF GCC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 372 REST OF GCC: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 373 REST OF GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 374 REST OF GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 375 REST OF GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 376 REST OF GCC: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 377 REST OF GCC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 378 REST OF GCC: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 379 REST OF GCC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 380 REST OF GCC: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 381 REST OF GCC: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 382 REST OF GCC: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 383 SOUTH AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 384 SOUTH AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 385 SOUTH AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 386 SOUTH AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 387 SOUTH AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 388 SOUTH AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 389 SOUTH AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 390 SOUTH AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 391 SOUTH AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 392 SOUTH AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 393 SOUTH AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 394 SOUTH AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 395 SOUTH AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 396 SOUTH AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 397 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 398 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 399 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 400 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 401 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 402 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 403 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 404 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 405 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 406 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 407 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 408 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 409 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 410 REST OF THE MIDDLE EAST & AFRICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 411 LATIN AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 412 LATIN AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 413 LATIN AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 414 LATIN AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 415 LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 416 LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 417 LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 418 LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 419 LATIN AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 420 LATIN AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 421 LATIN AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 422 LATIN AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 423 LATIN AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 424 LATIN AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 425 LATIN AMERICA: SECURITY TESTING MARKET, BY COUNTRY, 2019-2024 (USD MILLION)
- TABLE 426 LATIN AMERICA: SECURITY TESTING MARKET, BY COUNTRY, 2025-2031 (USD MILLION)
- TABLE 427 BRAZIL: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 428 BRAZIL: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 429 BRAZIL: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 430 BRAZIL: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 431 BRAZIL: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 432 BRAZIL: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 433 BRAZIL: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 434 BRAZIL: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 435 BRAZIL: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 436 BRAZIL: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 437 BRAZIL: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 438 BRAZIL: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 439 BRAZIL: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 440 BRAZIL: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 441 MEXICO: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 442 MEXICO: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 443 MEXICO: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 444 MEXICO: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 445 MEXICO: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 446 MEXICO: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 447 MEXICO: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 448 MEXICO: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 449 MEXICO: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 450 MEXICO: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 451 MEXICO: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 452 MEXICO: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 453 MEXICO: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 454 MEXICO: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 455 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 456 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 457 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 458 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 459 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2019-2024 (USD MILLION)
- TABLE 460 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE, 2025-2031 (USD MILLION)
- TABLE 461 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2019-2024 (USD MILLION)
- TABLE 462 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL, 2025-2031 (USD MILLION)
- TABLE 463 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2019-2024 (USD MILLION)
- TABLE 464 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY DEPLOYMENT MODE, 2025-2031 (USD MILLION)
- TABLE 465 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2019-2024 (USD MILLION)
- TABLE 466 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY ORGANIZATION SIZE, 2025-2031 (USD MILLION)
- TABLE 467 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2019-2024 (USD MILLION)
- TABLE 468 REST OF LATIN AMERICA: SECURITY TESTING MARKET, BY VERTICAL, 2025-2031 (USD MILLION)
- TABLE 469 OVERVIEW OF STRATEGIES ADOPTED BY KEY SECURITY TESTING VENDORS
- TABLE 470 SECURITY TESTING MARKET: DEGREE OF COMPETITION
- TABLE 471 SECURITY TESTING MARKET: SECURITY TESTING TYPE FOOTPRINT, 2025
- TABLE 472 SECURITY TESTING MARKET: DEPLOYMENT MODE FOOTPRINT, 2025
- TABLE 473 SECURITY TESTING MARKET: VERTICAL FOOTPRINT, 2025
- TABLE 474 SECURITY TESTING MARKET: REGIONAL FOOTPRINT, 2025
- TABLE 475 SECURITY TESTING MARKET: KEY STARTUPS/SMES, 2025
- TABLE 476 SECURITY TESTING MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES, BY SECURITY TESTING TYPE, 2025
- TABLE 477 SECURITY TESTING MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES, BY DEPLOYMENT MODE, 2025
- TABLE 478 SECURITY TESTING MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES, BY VERTICAL, 2025
- TABLE 479 SECURITY TESTING MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES, BY REGION, 2025
- TABLE 480 SECURITY TESTING MARKET: PRODUCT LAUNCHES AND ENHANCEMENTS, JANUARY 2023-FEBRUARY 2026
- TABLE 481 SECURITY TESTING MARKET: DEALS, JANUARY 2023-FEBRUARY 2026
- TABLE 482 IBM: COMPANY OVERVIEW
- TABLE 483 IBM: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 484 IBM: DEALS
- TABLE 485 OPENTEXT: COMPANY OVERVIEW
- TABLE 486 OPENTEXT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 487 OPENTEXT: PRODUCT LAUNCHES
- TABLE 488 CIGNITI TECHNOLOGIES: COMPANY OVERVIEW
- TABLE 489 CIGNITI TECHNOLOGIES: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 490 INTERTEK: COMPANY OVERVIEW
- TABLE 491 INTERTEK: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 492 INTERTEK: PRODUCT LAUNCHES
- TABLE 493 QUALITEST: COMPANY OVERVIEW
- TABLE 494 QUALITEST: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 495 BLACK DUCK: COMPANY OVERVIEW
- TABLE 496 BLACK DUCK: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 497 HCLSOFTWARE: COMPANY OVERVIEW
- TABLE 498 HCLSOFTWARE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 499 HCLSOFTWARE: DEALS
- TABLE 500 LEVELBLUE: COMPANY OVERVIEW
- TABLE 501 LEVELBLUE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 502 LEVELBLUE: DEALS
- TABLE 503 DXC TECHNOLOGY: COMPANY OVERVIEW
- TABLE 504 DXC TECHNOLOGY: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 505 DXC TECHNOLOGY: DEALS
- TABLE 506 EINFOCHIPS: COMPANY OVERVIEW
- TABLE 507 EINFOCHIPS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 508 CHECKMARX: COMPANY OVERVIEW
- TABLE 509 CHECKMARX: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 510 CHECKMARX: PRODUCT LAUNCHES
- TABLE 511 CHECKMARX: DEALS
- TABLE 512 HACKERONE: COMPANY OVERVIEW
- TABLE 513 HACKERONE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 514 HACKERONE: PRODUCT LAUNCHES
- TABLE 515 HACKERONE: DEALS
- TABLE 516 INVICTI: COMPANY OVERVIEW
- TABLE 517 INVICTI: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 518 INVICTI: PRODUCT LAUNCHES
- TABLE 519 INVICTI: DEALS
- TABLE 520 DATAART: COMPANY OVERVIEW
- TABLE 521 DATAART: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 522 COBALT: COMPANY OVERVIEW
- TABLE 523 COBALT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
- TABLE 524 COBALT: PRODUCT LAUNCHES
- TABLE 525 COBALT: DEALS
- TABLE 526 FACTOR ANALYSIS
List of Figures
- FIGURE 1 SECURITY TEST MARKET SEGMENTATION
- FIGURE 2 STUDY YEARS CONSIDERED
- FIGURE 3 MARKET SCENARIO
- FIGURE 4 GLOBAL SECURITY TESTING MARKET, 2019-2031 (USD MILLION)
- FIGURE 5 MAJOR STRATEGIES ADOPTED BY KEY PLAYERS IN SECURITY TESTING MARKET 2021-2026
- FIGURE 6 DISRUPTIVE TRENDS IMPACTING GROWTH OF SECURITY TESTING MARKET
- FIGURE 7 HIGH-GROWTH SEGMENTS & EMERGING FRONTIERS IN SECURITY TESTING MARKET, 2025
- FIGURE 8 ASIA PACIFIC TO REGISTER HIGHEST GROWTH DURING FORECAST PERIOD
- FIGURE 9 TECHNOLOGICAL ADVANCEMENTS, STRINGENT DATA PROTECTION TO DRIVE DEMAND FOR SECURITY TESTING
- FIGURE 10 NETWORK SECURITY TESTING SEGMENT TO ACCOUNT FOR LARGER MARKET SHARE DURING FORECAST PERIOD
- FIGURE 11 NETWORK PENETRATION TESTING SEGMENT TO ACCOUNT FOR LARGEST MARKET SHARE DURING FORECAST PERIOD
- FIGURE 12 WEB APPLICATION SECURITY TESTING SEGMENT TO ACCOUNT FOR LARGEST MARKET SHARE DURING FORECAST PERIOD
- FIGURE 13 RUNTIME APPLICATION SELF-PROTECTION (RASP) SEGMENT TO ACCOUNT FOR LARGEST MARKET SHARE DURING FORECAST PERIOD
- FIGURE 14 BFSI TO ACCOUNT FOR LARGEST MARKET SHARE DURING FORECAST PERIOD
- FIGURE 15 ASIA PACIFIC TO EMERGE AS BEST MARKET FOR INVESTMENT IN NEXT FIVE YEARS
- FIGURE 16 SECURITY TESTING MARKET: DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES
- FIGURE 17 PORTER'S FIVE FORCES ANALYSIS: SECURITY TESTING MARKET
- FIGURE 18 SECURITY TESTING MARKET: VALUE CHAIN ANALYSIS
- FIGURE 19 KEY PLAYERS IN SECURITY TESTING MARKET ECOSYSTEM
- FIGURE 20 AVERAGE SELLING PRICES OF KEY PLAYERS FOR TOP TWO TESTING TYPES (USD), 2025
- FIGURE 21 TRENDS/DISRUPTIONS IMPACTING CUSTOMERS' BUSINESSES
- FIGURE 22 LEADING GLOBAL SECURITY TESTING STARTUPS AND SMES, BY NUMBER OF INVESTORS AND FUNDING ROUNDS, 2021-2025
- FIGURE 23 NUMBER OF PATENTS GRANTED FOR SECURITY TESTING MARKET, 2016-2026
- FIGURE 24 REGIONAL ANALYSIS OF PATENTS GRANTED FOR SECURITY TESTING MARKET, 2024
- FIGURE 25 FUTURE APPLICATIONS OF SECURITY TESTING
- FIGURE 26 SECURITY TESTING MARKET: DECISION-MAKING FACTORS
- FIGURE 27 INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE USER TYPES
- FIGURE 28 KEY BUYING CRITERIA FOR TOP THREE USER TYPES
- FIGURE 29 ADOPTION BARRIERS AND INTERNAL CHALLENGES
- FIGURE 30 NETWORK SECURITY TESTING SEGMENT TO ACCOUNT FOR LARGEST MARKET SIZE DURING FORECAST PERIOD
- FIGURE 31 NETWORK PENETRATION TESTING SEGMENT TO ACCOUNT FOR LARGEST MARKET SIZE DURING FORECAST PERIOD
- FIGURE 32 WEB APPLICATION SECURITY TESTING SEGMENT TO HOLD LARGEST MARKET SIZE DURING FORECAST PERIOD
- FIGURE 33 STATIC APPLICATION SECURITY TESTING SEGMENT TO ACCOUNT FOR LARGEST MARKET SIZE DURING FORECAST PERIOD
- FIGURE 34 ON-PREMISES SEGMENT TO ACCOUNT FOR LARGER MARKET SIZE DURING FORECAST PERIOD
- FIGURE 35 LARGE ENTERPRISES SEGMENT TO ACCOUNT FOR LARGER MARKET SIZE DURING FORECAST PERIOD
- FIGURE 36 HEALTHCARE VERTICAL TO ACCOUNT FOR HIGHEST GROWTH RATE DURING FORECAST PERIOD
- FIGURE 37 ASIA PACIFIC TO GROW AT HIGHEST CAGR DURING FORECAST PERIOD
- FIGURE 38 NORTH AMERICA: MARKET SNAPSHOT
- FIGURE 39 ASIA PACIFIC: MARKET SNAPSHOT
- FIGURE 40 TOP FIVE PLAYERS DOMINATING MARKET IN LAST FIVE YEARS, 2020-2024 (USD MILLION)
- FIGURE 41 SHARE OF LEADING COMPANIES IN SECURITY TESTING MARKET, 2025
- FIGURE 42 BRAND COMPARISON
- FIGURE 43 SECURITY TESTING MARKET: COMPANY EVALUATION MATRIX (KEY PLAYERS), 2025
- FIGURE 44 SECURITY TESTING MARKET: COMPANY FOOTPRINT, 2025
- FIGURE 45 SECURITY TESTING MARKET: COMPANY EVALUATION MATRIX (STARTUPS/SMES), 2025
- FIGURE 46 SECURITY TESTING MARKET: COMPANY VALUATION OF KEY VENDORS, 2025 (USD BILLION)
- FIGURE 47 SECURITY TESTING MARKET: FINANCIAL METRICS OF KEY VENDORS, 2025
- FIGURE 48 IBM: COMPANY SNAPSHOT
- FIGURE 49 OPENTEXT: COMPANY SNAPSHOT
- FIGURE 50 CIGNITI TECHNOLOGIES: COMPANY SNAPSHOT
- FIGURE 51 INTERTEK: COMPANY SNAPSHOT
- FIGURE 52 HCLSOFTWARE: COMPANY SNAPSHOT
- FIGURE 53 DXC TECHNOLOGY: COMPANY SNAPSHOT
- FIGURE 54 SECURITY TESTING MARKET: RESEARCH DESIGN
- FIGURE 55 BREAKDOWN OF PRIMARY PROFILES, BY COMPANY TYPE, DESIGNATION, AND REGION
- FIGURE 56 KEY INSIGHTS FROM INDUSTRY EXPERTS
- FIGURE 57 DATA TRIANGULATION
- FIGURE 58 APPROACH 1 (SUPPLY SIDE): REVENUE OF SECURITY TESTING SOLUTIONS AND SERVICES FROM VENDORS
- FIGURE 59 APPROACH 1 (SUPPLY SIDE) ANALYSIS
- FIGURE 60 SECURITY TESTING MARKET ESTIMATION: RESEARCH FLOW
- FIGURE 61 APPROACH 2: BOTTOM-UP (DEMAND SIDE): PLATFORMS/SOLUTIONS/SERVICES










